The Translation Layer
How Law Becomes System Behavior
Introduction
Documentation Debt, Evidence Latency and Enforcement Drift, and the Oracle Problem have established the complete diagnostic: Documentation Debt explains how representational artifacts diverge from operational reality; Evidence Latency and Enforcement Drift explain how temporal displacement compounds that divergence; and the Oracle Problem identifies the irreducible trust boundary that every verification architecture must acknowledge. Together they constitute the problem statement for the architectural response.
The Architecture section presents that response. The Translation Layer, the Control Assertion Engine, and the Attestation Layer form the complete architecture through which legal obligation becomes system behavior, and system behavior becomes verifiable evidence. Each addresses specific failure modes established in the diagnostic section. They are designed to be read in sequence.
Compliance as infrastructure depends on one critical capability: the ability to convert ambiguous legal and contractual language into enforceable, testable, continuously verifiable system behavior.
This conversion does not happen automatically. It is not a single act of interpretation. It is not a policy memo. It is not a spreadsheet mapping exercise.
It is a governed, versioned, replayable transformation pipeline.
That pipeline is the Translation Layer.
The Translation Layer is the mechanical interface between human obligation and machine execution. It converts regulatory text into structured requirements, decomposes those requirements into atomic constraint units, generates control assertions, binds those assertions to telemetry, and maintains traceability and drift detection over time.
If the Control Plane enforces behavior, the Translation Layer defines what behavior must exist and why.
This chapter explains how that translation occurs, how it is validated, how it is governed, and how it is maintained.
The Structural Problem
Regulations and contracts are written in natural language. Natural language is inherently ambiguous. Terms such as reasonable, appropriate, adequate, timely, and proportional cannot be compiled into code.
Systems, by contrast, operate through deterministic instructions. They require structured inputs, explicit conditions, and defined failure states.
Compliance failures frequently occur not because enforcement is absent, but because interpretation was inconsistent, incomplete, undocumented, or allowed to drift.
The Translation Layer exists to close that gap.
It ensures that:
- Every enforceable control is traceable to an originating obligation
- Every interpretation decision is versioned
- Every ambiguity is surfaced, scored, and governed
- Every conflict is adjudicated through a structured workflow
- Every inherited or third-party control has explicit activation requirements
The Translation Layer does not write enforcement code. It defines what enforcement must do, how it is validated, and how it is governed.
System Boundary
Inputs
The Translation Layer receives:
- Regulations
- Contracts
- Internal policy
- Security frameworks
- Audit findings
- Risk decisions
- Authorized exceptions
- Data classification signals
- Provider attestations
Outputs
The Translation Layer produces:
- Control assertions
- Evidence specifications
- Evidence bindings
- Traceability graph entries
- Translation drift reports
- Adjudication records
- Exclusion records
- Boundary Hand-off Protocol records
The Translation Layer defines expected behavior and failure semantics. Enforcement systems execute that behavior. Evidence systems prove it.
Stage 1: Obligation Intake
Every obligation entering the system must become a canonical record.
An Obligation Record contains:
- Source
- Jurisdiction
- Effective date
- Scope
- Responsible owner
- Review cadence
- Risk classification
No obligation may proceed without full metadata.
Key metrics:
- Percent of obligations with complete metadata
- Time from intake to normalization
This stage establishes provenance. Without provenance, traceability collapses.
Stage 2: Obligation Normalization
Legal language is converted into structured requirement statements.
Each normalized obligation contains:
- Actor
- Action
- Object
- Condition
- Frequency
- Evidence expectation
- Interpretation class: deterministic, parameterized, or judgment-based
If interpretation class is judgment-based, a Decision Record is required. That record captures rationale, references, precedent alignment, and review cadence.
Ambiguity Scoring
The system assigns an ambiguity score using a deterministic rubric that detects open-textured legal qualifiers and conditional constructs.
Metrics include:
- Ambiguity score distribution
- Independent reviewer agreement rate
- Normalization cycle time
Ambiguity is not suppressed. It is quantified and governed.
Stage 3: Semantic Decomposition
Normalized obligations are decomposed into atomic translation units.
Each Translation Unit includes:
- Intent class
- Constraint type
- Subject
- Object
- Action
- Conditions
- Ambiguity flags
- Structured interpretation notes
- Taxonomy version reference
Minimum taxonomy domains include:
- Data handling
- Access control
- Logging and monitoring
- Encryption and key management
- Availability and resilience
- Change management
- Third-party controls
- Incident response
- Financial record integrity
Ontology Governance and Dependency Replay
The taxonomy itself is versioned.
The Taxonomy Registry maintains:
- Version identifier
- Change history
- Term ownership
- Backward compatibility policy
- Retrofit triggers
If taxonomy changes, the system triggers a Dependency Replay Process. All affected obligations, translation units, control assertions, and evidence bindings are re-evaluated.
Board metric: Taxonomy drift backlog size.
Language changes must not silently alter enforcement logic.
Stage 4: Control Assertion Generation
Each translation unit produces one or more machine-testable control assertions.
A Control Assertion contains:
- System component
- Required behavior
- Enforcement interface reference
- Failure condition
- Test method schema
- Scope tags
- Inheritance status
The assertion defines what must happen. It does not define how it is coded.
Coverage metric: Weight-adjusted obligation coverage ratio. Raw coverage percentages are insufficient. Coverage must be weighted by sufficiency.
Stage 5: Evidence Specification and Binding
A control is meaningless without evidence.
An Evidence Binding defines:
- Telemetry source
- Extraction method
- Schema version
- Integrity mechanism
- Validation test
- Semantic telemetry checks
Semantic Telemetry Drift
Telemetry can drift semantically without schema change. For example, a field may retain its name but alter its meaning.
The system must perform semantic checks using distribution analysis, type inference, sample inspection, and classification models.
Drift detection metrics:
- Mean time to drift detection
- Drift frequency per quarter
Weighted Sufficiency Scoring
Coverage is calculated using sufficiency weights.
Inputs to scoring include:
- Evidence freshness
- Evidence integrity strength
- Scope alignment
- Automation level
- Independence of evidence source
The scoring algorithm is versioned and auditable.
No inherited control may exceed the attestation weight cap unless live operational telemetry is bound.
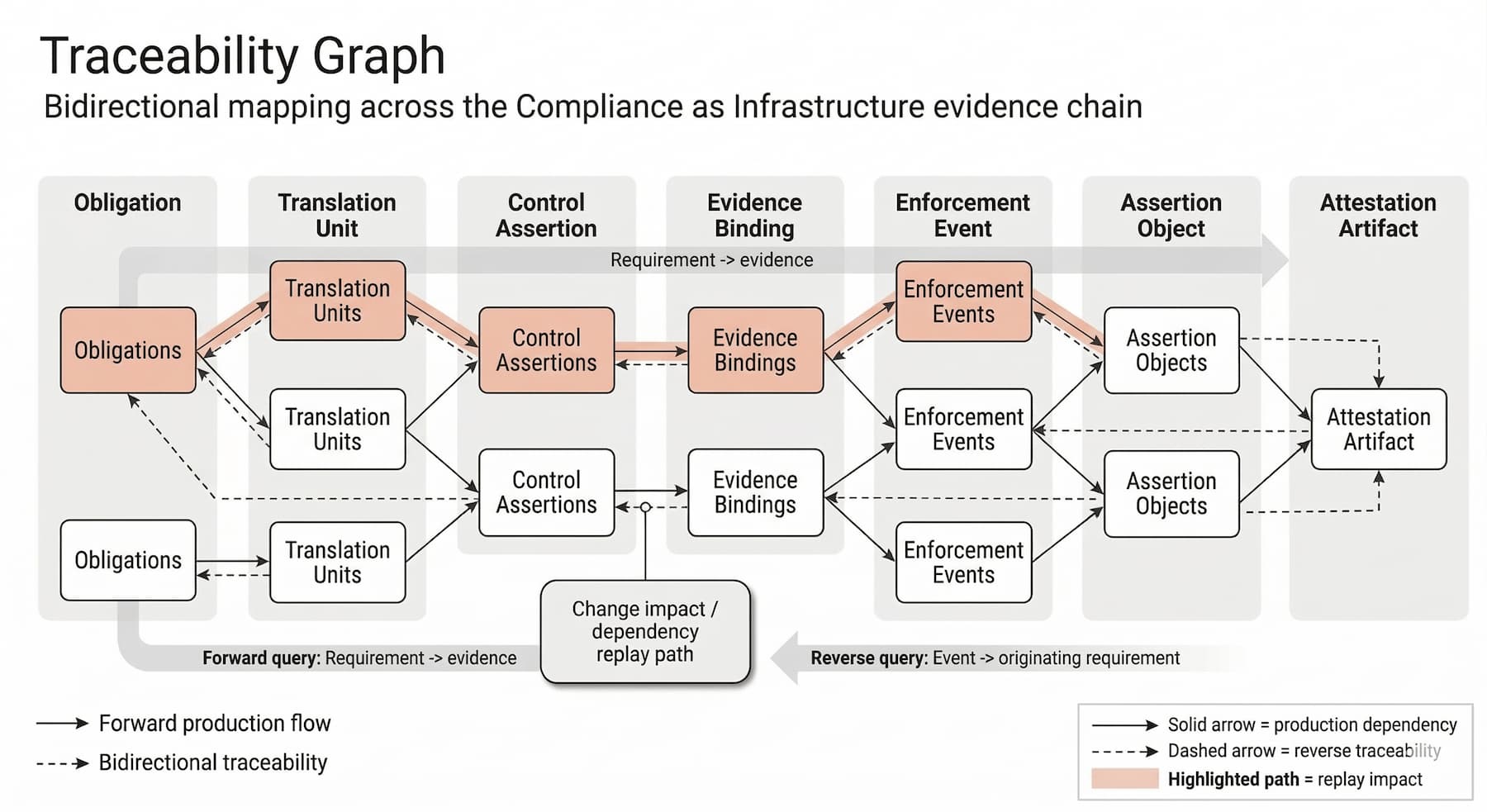
Stage 6: Traceability Graph Management
The traceability graph maintains bidirectional links:
Obligation → Translation Unit → Control Assertion → Evidence Binding
Required capabilities:
- Logical namespaces
- Scope tagging
- Weighted edge scoring
- Cycle detection
- Aggregation rules
- Board-level views
Primary KPI: Weight-adjusted translation coverage.
Stage 7: Drift Detection
Drift triggers include:
- Regulatory change
- Contract change
- Architecture change
- Telemetry schema change
- Data classification change
- New data onboarding
- Taxonomy version change
Each trigger produces a Translation Drift Report.
Compliance cannot be considered stable without drift monitoring.
Conflict Resolution Engine
The system assumes that some obligations are mutually unsatisfiable.
Conflict detection methods:
- Static logic analysis
- Telemetry collision
- Namespace overlap
- Constraint satisfaction failure
Conflict classes:
- Direct logic conflict
- Resource contention
- Jurisdictional overlap
- Operational drift
When active conflicts exist, system status becomes: Contested Compliance.
Required Artifact: Adjudication Record
Every conflict must produce a machine-readable Adjudication Record. The complete schema is reproduced below without alteration.
{
"artifact_type": "adjudication_record",
"schema_version": "1.0",
"adjudication_record_id": "AR-<uuid>",
"created_at": "<iso8601>",
"updated_at": "<iso8601>",
"status": "proposed | approved | rejected | superseded | expired",
"conflict": {
"conflict_id": "CRE-<uuid>",
"conflict_class": "direct_logic_conflict | resource_contention | jurisdictional_overlap | operational_drift",
"severity": "low | medium | high | critical",
"detected_by": "static_analysis | telemetry_collision | namespace_overlap",
"detected_at": "<iso8601>",
"object_refs": [
{
"object_id": "<stable_object_identifier>",
"object_type": "dataset | record | log_stream | key_material | account | service | infrastructure_component",
"scope_tags": ["Production", "EU-Region", "PCI-Scope"]
}
],
"graph_refs": {
"obligation_node_ids": ["OBL-<id>", "OBL-<id>"],
"translation_unit_ids": ["TU-<id>", "TU-<id>"],
"control_assertion_ids": ["CA-<id>", "CA-<id>"],
"evidence_binding_ids": ["EB-<id>", "EB-<id>"]
},
"collision_summary": {
"mutual_exclusivity_rule_id": "ME-<id>",
"description": "<short machine-safe summary>",
"conflicting_actions": [
{ "action": "delete", "condition": "<condition_ref_or_text>" },
{ "action": "retain", "condition": "<condition_ref_or_text>" }
]
}
},
"parties": {
"risk_owner": { "principal_id": "<id>", "name": "<string>", "org_unit": "<string>" },
"legal_sme": { "principal_id": "<id>", "name": "<string>", "org_unit": "<string>" },
"security_architect": { "principal_id": "<id>", "name": "<string>", "org_unit": "<string>" },
"control_engineer": { "principal_id": "<id>", "name": "<string>", "org_unit": "<string>" },
"audit_liaison": { "principal_id": "<id>", "name": "<string>", "org_unit": "<string>" }
},
"decision_inputs": {
"legal_priority_review": {
"precedence_score": {
"statutory_penalty_score": 0,
"contractual_liability_score": 0,
"enforcement_likelihood_score": 0,
"reputational_impact_score": 0,
"rationale": "<structured text>"
},
"references": [
{ "source_type": "regulation | contract | policy", "source_id": "<id>", "section_ref": "<string>" }
]
},
"impact_modeling": {
"option_A_priority_override": {
"failure_mode": "<string>",
"estimated_impact": { "financial": "<range_or_value>", "operational": "<string>", "legal": "<string>" }
},
"option_B_technical_bifurcation": {
"failure_mode": "<string>",
"estimated_impact": { "financial": "<range_or_value>", "operational": "<string>", "legal": "<string>" }
},
"option_C_compensating_control": {
"failure_mode": "<string>",
"estimated_impact": { "financial": "<range_or_value>", "operational": "<string>", "legal": "<string>" }
}
}
},
"determination": {
"chosen_path": "A_priority_override | B_technical_bifurcation | C_compensating_control",
"decision_statement": "<string>",
"effective_scope": {
"scope_tags": ["Production", "EU-Region"],
"environments": ["prod"],
"jurisdictions": ["EU", "US"],
"business_units": ["<string>"]
},
"authorized_exception": {
"exception_id": "EX-<id>",
"subordinate_obligation_ids": ["OBL-<id>"],
"exception_reason_code": "legal_conflict | technical_impossibility | transitional_state | third_party_dependency",
"time_bound": true
},
"technical_bifurcation": {
"bifurcation_required": false,
"pattern": "pseudonymization | tokenization | segmentation | dual_store | jurisdictional_sharding | access_partition",
"new_object_ids": ["<id>", "<id>"],
"implementation_owner": "<principal_id>"
},
"compensating_controls": [
{
"control_assertion_id": "CA-<id>",
"compensating_tag": true,
"risk_taxonomy_ref": "<risk_taxonomy_id>",
"evidence_spec_id": "ES-<id>",
"evidence_binding_id": "EB-<id>",
"sufficiency_weight": 0.0
}
],
"traceability_presentation": {
"graph_edge_type": "primary | dashed_compensating | override",
"weight_adjusted_coverage_impact": 0.0
}
},
"review_and_expiration": {
"review_cadence_days": 180,
"expiration_date": "<iso8601>",
"re_evaluation_trigger_conditions": [
"regulation_update",
"contract_update",
"system_arch_change",
"telemetry_schema_change",
"data_classification_change"
],
"supersedes_adjudication_record_id": "AR-<uuid>"
},
"attestation": {
"sign_off": [
{ "principal_id": "<id>", "role": "risk_owner", "signed_at": "<iso8601>" },
{ "principal_id": "<id>", "role": "legal_sme", "signed_at": "<iso8601>" }
],
"sign_off_hash": "<hash>",
"hash_algorithm": "sha256",
"immutability_target": "worm_store | git_tag | ledger_entry"
},
"audit_export": {
"export_ready": true,
"export_formats": ["oscal_json", "csv", "pdf_render"],
"redaction_profile": "internal | regulator | external_auditor"
}
}
Required Artifact: Boundary Hand-off Protocol
The full schema remains unchanged and is reproduced below in full fidelity.
{
"artifact_type": "boundary_handoff_protocol",
"schema_version": "1.0",
"bhp_id": "BHP-<uuid>",
"created_at": "<iso8601>",
"updated_at": "<iso8601>",
"status": "draft | approved | superseded",
"applies_to": {
"control_assertion_id": "CA-<id>",
"obligation_ids": ["OBL-<id>"],
"scope_tags": ["Production", "EU-Region", "PCI-Scope"],
"environments": ["prod"],
"jurisdictions": ["EU", "US"]
},
"shared_responsibility_boundary": {
"provider": {
"provider_name": "<string>",
"provider_service": "<string>",
"provider_account_id": "<string>",
"provider_artifact_refs": [
{
"artifact_type": "soc2 | iso27001 | pci_aoc | sig_lite | other",
"artifact_id": "<string>",
"valid_from": "<iso8601>",
"valid_to": "<iso8601>",
"refresh_cadence_days": 365
}
]
},
"handoff_point": {
"boundary_type": "management_plane | data_plane | identity_plane | key_plane | network_plane",
"handoff_description": "<string>",
"responsibility_split": {
"provider_responsibilities": ["<string>"],
"enterprise_responsibilities": ["<string>"]
}
}
},
"enterprise_activation_requirements": {
"required_configuration_knobs": [
{
"knob_id": "KNOB-<id>",
"knob_name": "<string>",
"knob_location": "provider_console | provider_api | iac_repo | policy_engine | app_config",
"expected_state": "<string>",
"validation_method": "api_query | config_snapshot | runtime_probe | policy_decision_record",
"validation_query_ref": "<string>",
"failure_if_missing": true
}
],
"required_runbooks": [
{
"runbook_id": "RB-<id>",
"title": "<string>",
"owner_principal_id": "<id>",
"execution_cadence_days": 90
}
],
"required_change_controls": [
{
"change_control_id": "CC-<id>",
"description": "<string>",
"approval_role": "risk_owner | security_architect | legal_sme"
}
]
},
"evidence_binding_requirements": {
"dual_evidence_model": {
"infrastructure_attestation": {
"required": true,
"evidence_binding_id": "EB-<id>",
"evidence_type": "attestation_document",
"sufficiency_weight_cap": 0.3
},
"operational_enforcement": {
"required": true,
"evidence_binding_id": "EB-<id>",
"evidence_type": "live_telemetry",
"minimum_refresh_interval_minutes": 1440
}
},
"telemetry_semantic_checks": [
{
"check_id": "TSC-<id>",
"field_name": "<string>",
"expected_semantics": "<string>",
"detection_method": "distribution_shift | type_inference | sample_inspection | classifier",
"trigger_on_change": true
}
],
"heartbeat_tests": [
{
"test_id": "HB-<id>",
"test_type": "key_plane | identity_plane | logging_plane",
"test_description": "<string>",
"frequency_minutes": 1440,
"pass_fail_criteria": "<string>",
"evidence_binding_id": "EB-<id>"
}
]
},
"anti_false_green_rules": {
"coverage_floor_rules": [
{
"rule_id": "COV-<id>",
"rule": "IF control_type = inherited AND any required_configuration_knobs missing THEN sufficiency_weight = 0.0"
},
{
"rule_id": "COV-<id>",
"rule": "IF only infrastructure_attestation present AND no operational_enforcement evidence THEN sufficiency_weight <= 0.3"
}
],
"cycle_detection": {
"required": true,
"algorithm": "dfs_no_ancestor_cycles",
"on_cycle_detected": "reject_dependency_link | escalate_to_risk_owner"
}
},
"approvals": {
"required_signoffs": [
{ "role": "security_architect", "principal_id": "<id>" },
{ "role": "control_engineer", "principal_id": "<id>" }
],
"optional_signoffs": [
{ "role": "risk_owner", "principal_id": "<id>" }
]
},
"export": {
"export_ready": true,
"export_formats": ["oscal_json", "csv"]
}
}
Conclusion
The Translation Layer produces the complete machine-testable constraint set that defines compliant system behavior at runtime. The Control Assertion Engine that follows consumes those translated constraints directly, evaluating actual runtime behavior against them on a continuous basis. Constraint quality in the Translation Layer determines the precision and reliability of every assertion the CAE produces, establishing a direct dependency between translation integrity and enforcement accuracy.