The Oracle Problem
Why Compliance Infrastructure Always Terminates at a Trust Boundary
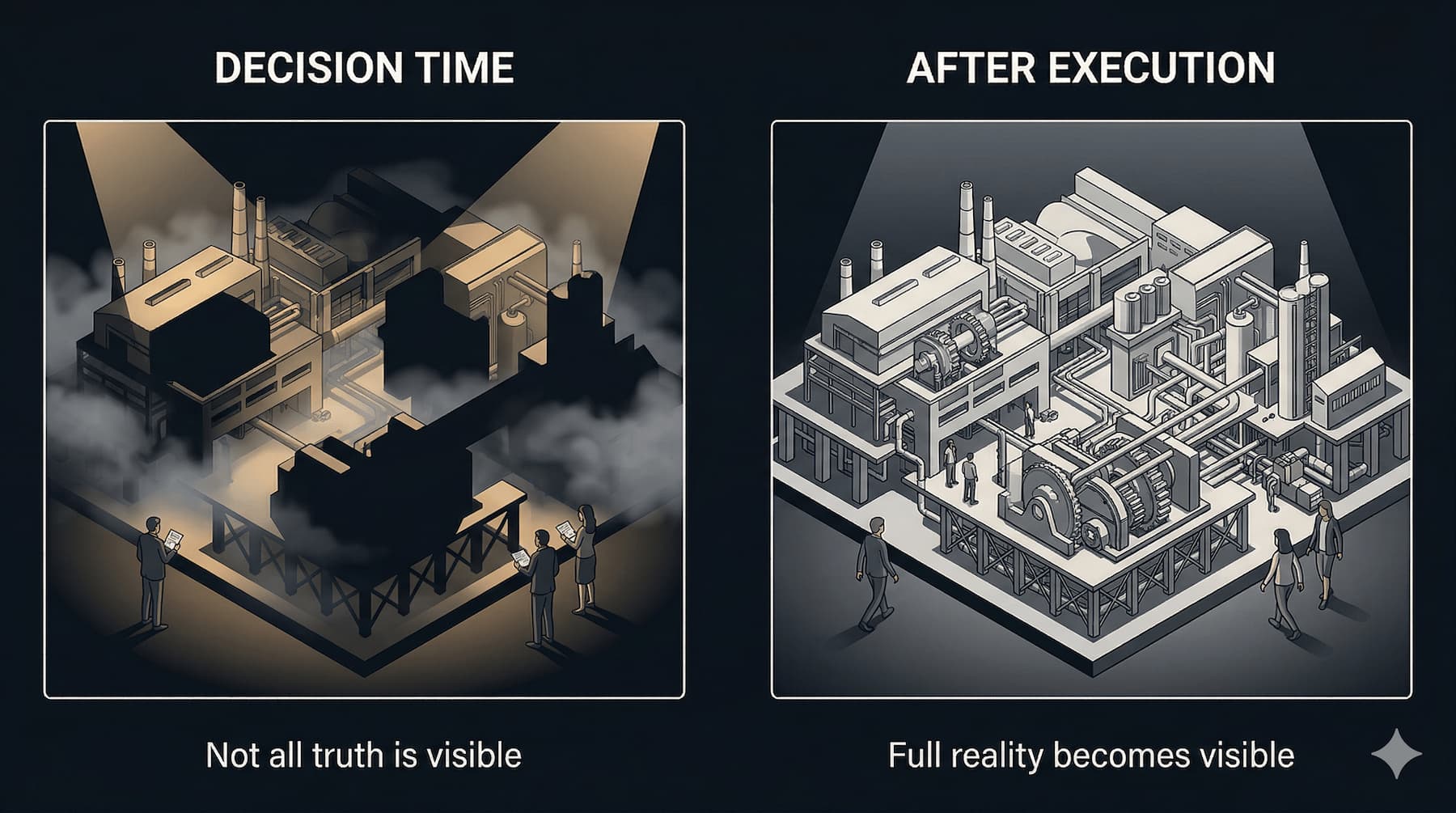
Evidence Latency and Enforcement Drift established that compliance evidence describes the past rather than the present — that evidence latency and enforcement drift together produce a sustained gap between system behavior and what verification systems can observe. This section addresses the deeper structural problem that remains even when that gap is minimized: every verification architecture, no matter how continuously instrumented, must eventually depend on facts it cannot independently derive. That dependency is the Oracle Problem. This section defines the Oracle Problem, maps the locations in a compliance architecture where oracle boundaries appear, examines the failure modes that arise when those boundaries are unacknowledged, and describes the design principles for governing them. The reader will understand why the Oracle Problem cannot be engineered away — only located deliberately, minimized, and disclosed.
Section 1 - The Shift From Audit to Infrastructure Verification
Traditional compliance verification is a documentation process. An auditor reviews records, interviews control owners, samples transactions, and produces an opinion about whether controls operated effectively during a defined period. The opinion is credible to the extent that the auditor is credible, the documentation is complete, and the sampling methodology is sound. None of these inputs derive from the operational system itself. They derive from representations of it.
Infrastructure-based compliance verification changes the source of evidence. Instead of representations assembled after the fact, compliance assertions are derived from system telemetry produced at the moment of control execution. The control plane generates evidence as a byproduct of operation. Verification engines consume that evidence and produce compliance assertions continuously rather than periodically.
This shift is architecturally significant. It changes compliance from an interpretive process to a computational one. It compresses the interval between control execution and compliance assertion. It reduces reliance on human attestation and documentation assembly. And it makes compliance verification a measurable property of a running system rather than a judgment about a historical period.
But infrastructure-based verification does not eliminate the fundamental problem it appears to solve. The question of whether a system's observable state accurately represents its actual behavior - and whether the mechanisms producing that state can be fully trusted - remains. This is the Oracle Problem.
The Oracle Problem is not unique to compliance. It appears in distributed systems, in financial markets, in autonomous systems, and in any domain where a verification mechanism must consume facts it cannot independently derive. In compliance infrastructure, it appears at every boundary where system-generated evidence depends on inputs, attestation artifacts, or observations that originate outside the verifying system's direct observation.
Understanding the Oracle Problem is a prerequisite for designing verification systems that are architecturally honest about their limitations. Systems that do not account for oracle dependency do not eliminate trust assumptions. They obscure them.
Section 2 - What Verification Actually Means
Precision in terminology matters here. The words validation, attestation, evidence, and verification are frequently used interchangeably in compliance contexts. They describe distinct mechanisms with distinct properties.
Validation. Mathematical or logical verification derived from deterministic system state. A hash comparison validates data integrity. A cryptographic signature validates provenance. A formal proof validates that a program satisfies a specification. Validation does not require trust in an external party. It requires only the relevant inputs and the verification algorithm. If the inputs are correct and the algorithm is sound, the validation result is deterministic.
Evidence. A record of system activity produced at the time of execution. An event log entry, a control execution trace, a policy evaluation output - these are evidence artifacts. Evidence generation converts runtime activity into records that can subsequently be consumed by a verification layer. Evidence quality depends on the fidelity of the instrumentation producing it and the integrity of the storage mechanism preserving it.
Attestation. An assertion that an event occurred or that a control executed. Attestation artifacts may be produced by automated systems or by humans. Human attestation reflects an individual's representation of their activity or judgment. Hardware attestation derives from physically constrained execution environments. Cryptographically signed attestation artifacts bind assertions to specific keys, enabling accountability for assertion accuracy. In each case, the consumer must extend trust to the attesting party, because the assertion cannot be independently recomputed from system state alone.
Verification. The process of determining whether system behavior satisfied defined constraints. Verification consumes evidence and attestation artifacts, applies a verification logic, and produces compliance assertions. Depending on the architecture, verification may be predominantly validative - relying on derivable system state - or predominantly attestation-dependent - relying on external assertions.
The Oracle Problem arises when verification depends on attestation artifacts that cannot be validated. The verifier must accept assertions as true without the capacity to recompute them from first principles. This dependency is the structural feature that defines the oracle relationship.
Section 3 - The Oracle Boundary
The term "oracle" in formal systems denotes a mechanism that answers questions which cannot be resolved by the querying system's own computation. In compliance infrastructure, an oracle is any mechanism that supplies facts not derivable from the consuming system's internal state.
The Oracle Problem in compliance is a boundary problem, not a philosophical recursion. It does not posit an infinite regress of verification layers, each requiring validation by the next. It identifies the specific location in a verification architecture where derivable truth ends and trusted assertion begins. That location is the oracle boundary.
The oracle boundary is where verification stops being mechanical and starts being trusted.
Critically, the existence of an oracle boundary is not a design failure. Every verification system has one. The question is where it sits and how it is governed. A system that derives compliance assertions entirely from hardware-attested execution traces has pushed the oracle boundary down to the hardware layer. A system that derives compliance assertions from auditor sign-off has placed the oracle boundary at the institutional layer. Both systems have oracle dependencies. They differ in where those dependencies are located and how reliably those locations can be governed.
The practical design objective is not to eliminate the oracle boundary but to:
- Locate it - identify it explicitly within the architecture
- Minimize it - reduce the surface area it occupies
- Govern it - define the mechanisms that operate at that boundary
- Disclose it - make the trust assumptions transparent and auditable
A verification architecture that does not identify its oracle boundary does not lack one. It has simply failed to account for it.
Section 4 - Where Oracles Appear in Compliance Systems
Oracle dependencies appear at multiple locations across a compliance infrastructure stack. Identifying them is the first step toward managing them.
External Data Feeds. Many compliance controls depend on reference data that originates outside the operational system. Sanctions lists, regulatory thresholds, counterparty classifications, and jurisdictional flags are examples. When a control evaluates a transaction against an external list, the control outcome depends on the accuracy and currency of that list. The operational system cannot independently verify that the list is correct. It must trust the data source.
Human Attestations. Control frameworks frequently include controls that depend on human judgment or confirmation. A manager certifying that access rights are appropriate, a compliance officer attesting to the completeness of a risk assessment, or an engineer confirming that a configuration change was reviewed - these are human attestations. They cannot be derived from system state. They reflect an individual's representation of their activity or judgment. The verification system that accepts them must trust the attesting individual and the process that produced the human attestation.
Third-Party Control Assertions. In distributed operating environments, organizations rely on controls operated by third parties - cloud providers, payment processors, custodians, managed service providers. When a compliance assertion depends on a control that operates in a third party's environment, the verifying organization cannot directly observe control execution. It must accept the third party's institutional attestation, typically formalized as a SOC report or equivalent certification. The third party is an oracle.
Environmental and Physical Signals. Some compliance requirements involve physical conditions - temperature in a data storage environment, physical access to secure areas, or geographic location of personnel or systems. Sensors, badge readers, and GPS systems produce these signals. The verification system must trust that the sensor network is accurate, tamper-resistant, and correctly integrated. Each sensor is an oracle.
Off-Chain and Off-System Information. When compliance decisions depend on information that exists outside the operational system - a signed contract, a regulatory filing, a legal opinion, a business relationship - that information must be ingested or referenced from an external source. The integrity of that ingestion path is an oracle dependency.
Section 5 - Why Verification Chains Cannot Be Infinite
A common informal response to oracle dependency is layering: add another verification system to validate the first, add another to validate the second, and continue until confidence is sufficient. This approach extends the verification chain but does not resolve the oracle problem. It relocates it.
Every verification layer is itself a system that can be questioned. A monitoring system that validates control execution is itself subject to compromise, misconfiguration, or oracle dependency. The chain of verification can be extended, but it must eventually terminate. Where it terminates is the trust anchor.
Trust anchors exist in three broad categories.
Cryptographic Trust Anchors. Cryptographic mechanisms allow verification that is computationally grounded rather than institutionally dependent. A cryptographic hash anchors data integrity. A digital signature anchors provenance. A zero-knowledge proof anchors constraint satisfaction without revealing underlying data. These mechanisms derive their reliability from mathematical properties rather than from the trustworthiness of any particular institution. Their oracle boundary is the mathematical primitive - the assumption that the underlying cryptographic construction is sound.
Hardware Trust Anchors. Hardware-based verification mechanisms - trusted execution environments, secure enclaves, TPM chips, and measured boot sequences - ground verification in physical constraints that are harder to compromise than software. When a compliance assertion is derived from a hardware-attested execution trace, the oracle boundary is pushed down to the hardware manufacturer and the supply chain.
Institutional Trust Anchors. When technical verification cannot fully resolve a trust question, verification chains terminate in governance. Independent auditors, regulatory bodies, certification authorities, and legal frameworks supply institutional trust anchors. These mechanisms do not produce mathematical proofs. They produce credible assertions backed by professional accountability, regulatory authority, and legal consequence. The oracle boundary terminates at the institution and the governance framework validating it.
All three categories of trust anchor have failure modes. Cryptographic systems can be undermined by key compromise, implementation vulnerabilities, or algorithmic weaknesses. Hardware systems can be compromised at the manufacturing or supply chain layer. Institutional systems can be undermined by conflicts of interest, resource constraints, or governance failures.
The implication is not that trust anchors are unreliable. It is that every trust anchor must be governed, and that governance must be proportionate to the risk exposure created by oracle dependency at that layer.
Section 6 - Failure Modes of Oracle Dependency
Oracle dependency produces identifiable failure modes in compliance infrastructure. Each failure mode represents a class of verification breakdown that cannot be detected by examining the verification system's internal state.
Assertion Without Derivation. A verification system accepts an attestation artifact that it cannot independently recompute from system state. The assertion is treated as evidence, but no evidence-generation mechanism validates it. The compliance assertion produced by the verification engine reflects the attestation artifact's accuracy, not the system's actual behavior. If the assertion is incorrect - due to error, misrepresentation, or system malfunction - the compliance assertion is incorrect, and the verification system cannot detect this.
Verification Chain Extension Without Terminus. Organizations respond to oracle dependency by adding verification layers. A control engine is validated by a monitoring system, which is validated by an audit system, which is validated by an independent monitor. Each layer adds operational cost and increases apparent confidence. But if the chain is extended without defining a trust anchor, the oracle problem is not resolved - it is deferred. The chain grows, but verification reliability does not necessarily increase. In some architectures, chain extension introduces additional failure points without commensurate reliability improvement.
Oracle Substitution. A system replaces deterministic control enforcement with human review or narrative human attestation. This occurs frequently when automated control execution is considered impractical or when control owners prefer judgment-based processes. The substitution trades deterministic verifiability for institutional reliability. This trade may be acceptable, but it must be made explicitly and its implications understood. When oracle substitution occurs without recognition, verification systems produce compliance assertions that appear mechanically grounded but are actually attestation-dependent.
Data Ingestion Integrity Failure. Oracle dependency at data ingestion boundaries is a common and underappreciated failure mode. A compliance control consumes external data - a regulatory list, a pricing feed, a counterparty status - without validating the integrity of the ingestion path. The control executes correctly against the data it receives. But if the data is stale, corrupted, manipulated, or incompletely transmitted, the control outcome is incorrect, and the compliance assertion reflects that incorrect input. The verification system has no mechanism to detect this failure, because it has no access to the authoritative external state against which to compare.
Temporal Drift. Verification reflects system state at time T1. System behavior evolves continuously. If the interval between control execution and compliance assertion is significant, the compliance assertion may not reflect current system behavior. Oracle latency - the delay between an event occurring and the oracle reporting it - compounds this problem. A verification system that depends on an oracle with high latency will produce compliance assertions that lag system state. Enforcement drift accumulates in the interval.
Governance Blind Spots. When oracle dependencies are not explicitly identified in system architecture, governance mechanisms cannot be designed to address them. Audit procedures that review the verification layer without examining oracle reliability will not detect failures at the oracle boundary. Risk assessments that evaluate control design without examining data ingestion integrity will not surface exposure at that layer. Governance blind spots are a direct consequence of unrecognized oracle dependencies.
Section 7 - Measuring Oracle Exposure
Oracle dependency can be characterized through measurable signals. These signals do not eliminate oracle dependency, but they allow organizations to assess their exposure and prioritize remediation.
Assertion Density. Assertion density measures the proportion of compliance claims that cannot be derived from internal system state. A verification architecture with high assertion density relies heavily on attestation artifacts rather than evidence artifacts. High assertion density is not inherently a failure, but it indicates high oracle exposure and should trigger scrutiny of the governance mechanisms protecting those assertions.
External Data Dependency Ratio. This metric expresses the percentage of verification inputs sourced externally relative to total verification inputs. A high external dependency ratio indicates that a large portion of compliance assertions depend on the accuracy and integrity of external data sources. Each external source is a potential oracle failure point.
Reconciliation Frequency. Frequent reconciliation between verification systems indicates that those systems diverge regularly. Divergence reflects oracle inconsistency - multiple systems are consuming facts about the same events and producing different results. High reconciliation frequency is a signal of degraded oracle reliability.
Verification Latency. Verification latency measures the delay between control execution and the production of a compliance assertion. High latency increases the window during which system behavior can diverge from the verified state. Latency thresholds should be defined relative to the regulatory or operational requirements of the control.
Multi-Oracle Divergence. When independent oracle sources are consulted for the same fact, divergence between them indicates fidelity degradation. A system that detects regular divergence between independent oracles has identified a signal requiring investigation. Either the fact itself is contested, the sources are using different observation windows, or one or more sources are failing.
Oracle Fidelity. Oracle fidelity is the proportion of oracle assertions subsequently validated against ground truth - typically through audits, reconciliation, or downstream verification - that prove accurate. Fidelity measurement requires a mechanism for post-hoc comparison, which is not always available. Where it can be constructed, oracle fidelity provides a quantitative basis for assessing oracle reliability over time.
Governance Override Frequency. Frequent human overrides of automated verification signals indicate that the verification system is producing results that human operators do not trust. This may reflect genuine errors in the verification logic, or it may reflect a mismatch between the verification system's rule set and actual organizational intent. In either case, high override frequency indicates that governance has partially displaced automated verification, increasing attestation dependency.
Section 8 - Designing Around the Oracle Problem
Oracle dependency cannot be eliminated. But verification architectures can be designed to minimize oracle surface area, locate oracle boundaries explicitly, and govern those boundaries appropriately.
Deterministic Evidence Generation. Systems should be instrumented to produce verifiable state transitions rather than narrative reports. Event sourcing architectures generate an append-only log of system events from which state can be reconstructed at any point in time. Immutable audit logs with integrity protections prevent post-hoc modification. Execution traces capture the specific path through control logic that produced a given outcome. These mechanisms produce evidence artifacts that can be independently verified against system state, reducing dependence on attestation.
Cryptographic Anchoring. Evidence artifacts should be cryptographically anchored to prevent tampering and establish provenance. Hash chaining links sequential records such that modification of any record is detectable. Merkle tree structures allow efficient verification of individual records within a large dataset without retrieving the entire set. Zero-knowledge proof systems allow a prover to demonstrate that a constraint was satisfied without revealing the underlying data, enabling verification in privacy-sensitive contexts. Cryptographically signed attestation artifacts bind assertions to specific keys, enabling accountability for attestation accuracy.
Hardware Roots of Trust. Verification chains should terminate in trusted execution boundaries where technically feasible. Secure enclaves provide isolated execution environments whose integrity can be attested by hardware-level mechanisms. TPM attestation allows systems to produce cryptographically verifiable claims about their boot state and software configuration. Measured boot sequences establish a chain of integrity measurements from firmware through operating system to application. These mechanisms push the oracle boundary down to hardware, where the trust assumptions are more constrained and the attack surface is more limited.
Multi-Oracle Aggregation. Where a single oracle source carries significant risk, verification systems should aggregate across multiple independent sources. Consensus-based verification requires agreement across a threshold of independent attestors before accepting a claim. Majority validation rejects claims supported by fewer than a defined proportion of sources. Economic mechanisms such as slashing - in which attestors bear financial penalties for incorrect assertions - create incentive alignment between oracle accuracy and oracle incentives. Multi-oracle architectures do not eliminate oracle dependency, but they distribute it and reduce the impact of any single oracle failure.
Continuous Verification. Point-in-time verification creates temporal gaps during which enforcement drift accumulates undetected. Continuous verification architectures consume system telemetry in near-real time and maintain an ongoing compliance assertion rather than producing periodic opinions. This approach requires investment in telemetry infrastructure and real-time verification capacity, but it substantially reduces the verification latency that enables temporal drift.
Separation of Evidence from Interpretation. Evidence generation and compliance conclusion should be architecturally separated. A control execution trace that is produced, preserved, and transmitted independently of the compliance assertion derived from it can be verified independently of the assertion engine. If evidence and interpretation are generated by the same system, a failure in that system can simultaneously corrupt the evidence base and the compliance conclusion without detection.
Section 9 - Infrastructure and Institutional Trust
A verification architecture built on deterministic evidence, cryptographic anchoring, and hardware roots of trust substantially narrows oracle surface area. It does not close it. Technical verification always terminates. When it does, institutional governance takes over.
Institutional governance mechanisms - independent audits, regulatory examinations, certification processes, accountability frameworks - supply the trust anchors that technical systems cannot provide. They do not operate with cryptographic precision. They operate with professional accountability, legal authority, and organizational consequence. These are different properties, but they are not weaker ones in all contexts. Legal accountability and regulatory authority are, in some respects, more robust enforcement mechanisms than cryptographic proofs, because they operate across system boundaries and attach consequences to behavior rather than just to computation.
The design implication is not that governance substitutes for infrastructure, or that infrastructure substitutes for governance. It is that they are complementary verification mechanisms with different properties and different failure modes.
Infrastructure verification provides high-frequency, low-latency compliance assertions; reduced dependence on human attestation; mechanically auditable evidence chains; and scalable verification capacity.
Institutional governance provides authority to define what constitutes compliance; accountability mechanisms for verification failures; interpretive capacity for novel or contested situations; and legitimacy that technical systems alone cannot supply.
Compliance infrastructure must be designed to support institutional oversight, not to replace it. This means verification systems must expose audit trails that are accessible to external reviewers. It means governance procedures must be documented and verifiable rather than assumed. It means accountability structures must be defined for oracle failures, human attestation errors, and enforcement drift events. And it means the oracle boundaries of the verification architecture must be disclosed to the governance layer that is responsible for managing them.
Organizations that deploy compliance infrastructure without designing for institutional integration will encounter a specific class of failure: their verification systems will become opaque to regulators and auditors, not because the systems are inadequate, but because the systems were not designed to surface their trust assumptions to external review.
Section 10 - Transition to Implementation
The preceding sections establish the structural context for the implementation sections that follow.
The Oracle Problem defines why verification infrastructure cannot be designed as a closed system. Every verification architecture has a trust boundary. The purpose of infrastructure design is to locate that boundary deliberately, minimize the surface area it occupies, govern the mechanisms that operate at it, and make the trust assumptions transparent to institutional oversight.
Two implementation mechanisms address specific components of this architecture.
The Control Assertion Engine operationalizes the verification layer. It consumes evidence artifacts generated by operational and control systems, applies constraint logic, and produces compliance assertions. Its design must account for the oracle dependencies introduced at evidence ingestion boundaries and the governance mechanisms required to validate those inputs.
The Attestation Layer manages the oracle boundary directly. It provides a structured mechanism for ingesting, validating, and recording attestation artifacts from internal and external sources. Its design determines how the verification system handles assertions it cannot independently derive - which claims it accepts, from which sources, under which governance conditions, and with what audit trail.
Together, these mechanisms implement the verification architecture described in this section. They do not solve the Oracle Problem. They operationalize a disciplined approach to managing it.