Terminology Glossary
Compliance as Infrastructure
This glossary covers all defined technical terms in the Compliance as Infrastructure manuscript. Terms are organized by conceptual domain. Each entry includes the canonical term, its definition as used in the manuscript, and the location of its first significant appearance.
Terminology normalization note: One term was normalized from the v3 manuscript. "Control Assertion Systems" (a section header in Documentation Debt) was updated to "Control Assertion Engine" to match the canonical component name used throughout the Architecture section. This change is the only edit made in producing draft v4. All other terminology is preserved as authored.

Conceptual Framework
| Term | Definition | First Appears |
|---|---|---|
| Compliance as Infrastructure | The embedding of regulatory and contractual constraints directly into the execution and orchestration layers of production systems, such that compliance is a continuously evaluated property of the system rather than a periodically declared status. | Category Foundation (Introduction) |
| Trust Gap | The structural gap between what systems actually do at runtime and what external parties can independently confirm about that behavior. Arises from the mismatch between continuous system change and periodic verification cadence. | Trust Gap |
| Trust Substitution | The practice of replacing direct verification of system behavior with proxy trust signals (certifications, third-party attestation, audit reports) when continuous independent verification is not feasible. | Trust Gap - Trust Substitution section |
| Point-in-Time Model | The traditional compliance approach in which systems are declared compliant at a specific moment through periodic audit, documentation review, and evidence sampling - without continuous state verification. | Category Foundation - The Failure of the Point-in-Time Model |
| Enforcement Drift | The divergence between defined compliance constraints and the behavior actually occurring in operational systems over time. Accumulates through continuous system change, delayed evidence generation, and interpretation delay. | Evidence Latency and Enforcement Drift, Section 4 |
| Execution Drift | Divergence between defined operational constraints and actual system behavior, where the policy is correctly defined but the system is not operating in conformance with it. A detection and remediation problem. | Evidence Latency and Enforcement Drift, Section 5 (Execution Drift and Policy Drift) |
| Policy Drift | Divergence between an organization's documented compliance policies and the regulatory obligations those policies are intended to satisfy. The systems may conform to internal policy, but the policy itself no longer reflects current regulatory requirements. | Evidence Latency and Enforcement Drift, Section 5 (Execution Drift and Policy Drift) |
| Audit Theater | The condition in which compliance artifacts satisfy the formal requirements of an audit process while failing to represent the actual compliance state of operational systems. The structural outcome of applying documentation-based compliance to dynamic environments. | Documentation Debt, Section 5 |
| Visibility Inversion | The structural distortion in which auditors observe documentation (which describes intended design) rather than operational system behavior, so that a system can satisfy audit review while experiencing significant control failures. | Documentation Debt, Section 6 |
| Overlay (Compliance Overlay) | A compliance implementation that observes or reports on system behavior after execution but does not sit in the execution path and does not shape that behavior. Distinguished from infrastructure-embedded compliance. | Category Foundation - From Overlay to Inline Enforcement |
| Circular Validation | An architectural risk in which the entity generating compliance evidence also controls the verification of that evidence, structurally predisposing evidence to confirm compliance rather than accurately measure it. | Evidence Latency and Enforcement Drift, Section 7 |
| Contested Compliance | The system status that applies when active, unresolved conflicts exist between mutually unsatisfiable obligations. Requires an Adjudication Record and prevents the system from reporting a clean compliance state. | Translation Layer, Conflict Resolution Engine |
Failure Mechanics
| Term | Definition | First Appears |
|---|---|---|
| Documentation Debt | The systematic divergence between descriptive compliance artifacts (documentation) and the actual behavior of operational systems. Accumulates through change velocity mismatch, maintenance cost scaling, representational compression, and audit substitution. | Documentation Debt, Section 3 |
| Evidence Latency | The time gap between system behavior and the moment when verifiable compliance evidence describing that behavior becomes available for evaluation. Comprises two independent dimensions: Signal Latency and Semantic Latency. | Evidence Latency and Enforcement Drift, Section 2 |
| Signal Latency | The delay between the execution of system behavior and the generation or collection of operational signals describing that behavior (logs, telemetry, configuration snapshots). The dimension most commonly addressed by technical investment. | Evidence Latency and Enforcement Drift, Section 2 (Signal Latency) |
| Semantic Latency | The delay between the availability of evidence and the ability of institutions to determine whether that evidence represents compliant or non-compliant behavior. Emerges from the interpretive process, not from technical pipeline delays. | Evidence Latency and Enforcement Drift, Section 2 (Semantic Latency) |
| Oracle Problem | The irreducible verification limit that arises when a compliance infrastructure system depends on facts, attestations, or observations that originate outside the verifying system's direct observation and cannot be independently derived. | Oracle Problem, Section 1 |
| Oracle Boundary | The specific location in a verification architecture where derivable truth ends and trusted assertion begins - where verification stops being mechanical and starts being trusted. | Oracle Problem, Section 3 |
| Oracle Substitution | The replacement of deterministic control enforcement with human review or narrative human attestation, trading deterministic verifiability for institutional reliability. | Oracle Problem, Section 6 |
| Oracle Fidelity | The proportion of oracle assertions subsequently validated against ground truth that prove accurate. A quantitative basis for assessing oracle reliability over time. | Oracle Problem, Section 7 |
Four-Layer Compliance Architecture
| Term | Definition | First Appears |
|---|---|---|
| Control Execution Layer (Layer 1) | The layer where operational behavior occurs: infrastructure configuration, deployment pipelines, authentication systems, data access enforcement, and runtime policy enforcement. Source of system state transitions. | Documentation Debt, Section 2 |
| Evidence Generation Layer (Layer 2) | The layer that captures telemetry produced by control execution: logs, metrics, audit trails, event streams, and state snapshots. Records what actually happened at the Control Execution Layer. | Documentation Debt, Section 2 |
| Documentation Layer (Layer 3) | The layer of human-readable artifacts describing how systems are expected to behave: policies, procedures, architecture diagrams, control narratives, and runbooks. Describes design intent, not actual behavior. | Documentation Debt, Section 2 |
| Audit Observation Layer (Layer 4) | The layer at which external observers (auditors, regulators, insurers, certification bodies) evaluate compliance by examining artifacts. In traditional compliance, auditors predominantly examine Layer 3 artifacts. | Documentation Debt, Section 2 |
| Prospective Documentation | Policies, procedures, architecture descriptions, and control narratives that describe how a system is intended to operate. Establishes intent but does not confirm execution. | Trust Gap - The Verification Limits of Documentation |
| Retrospective Artifacts | Operational records such as logs, deployment histories, system state captures, and control outputs that reflect what a system actually did. Constitute evidence of runtime behavior. | Trust Gap - The Verification Limits of Documentation |
Architecture Components
| Term | Definition | First Appears |
|---|---|---|
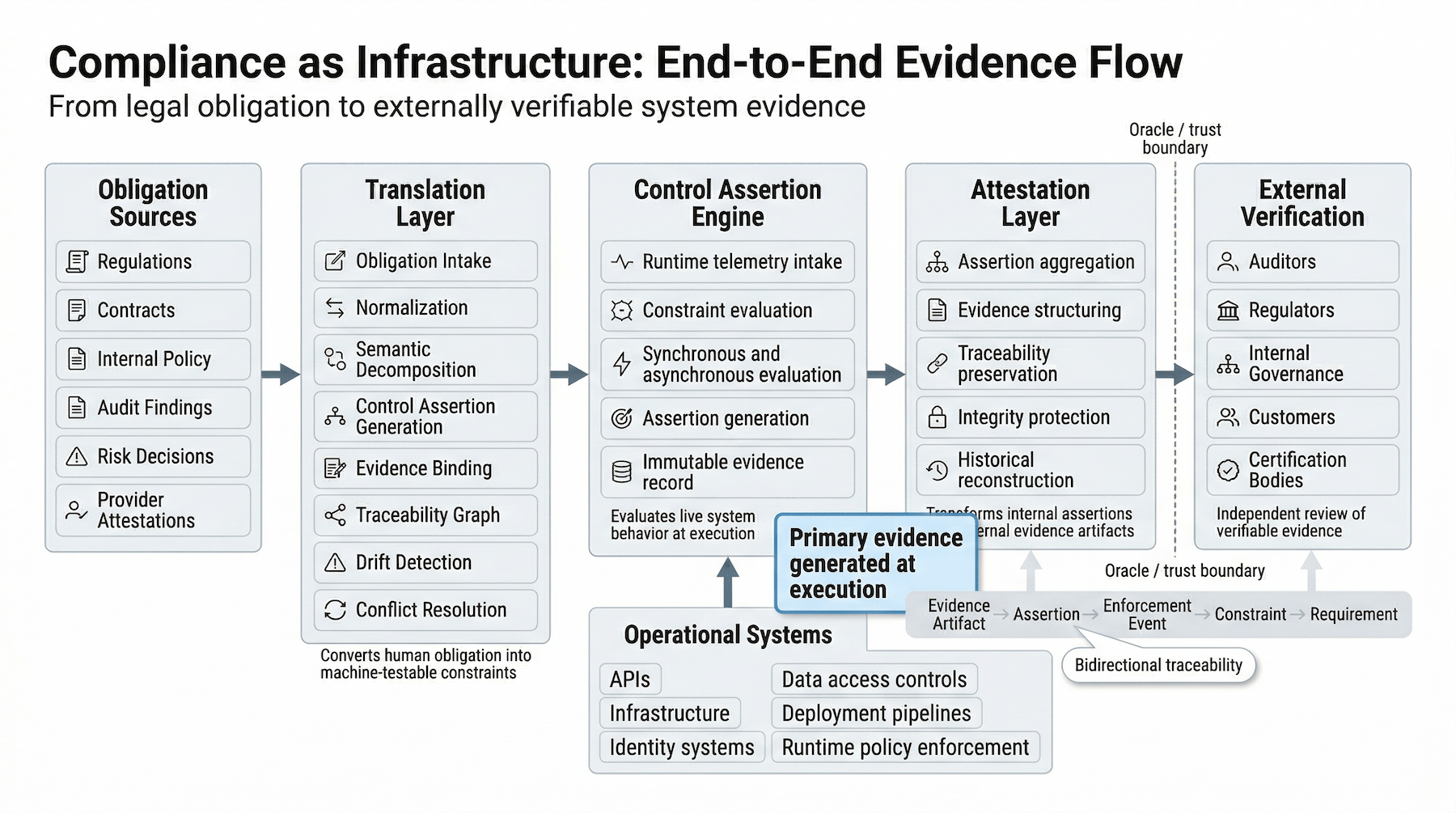
| Translation Layer | The governed, versioned, replayable transformation pipeline that converts regulatory and contractual obligations into machine-executable control assertions. The mechanical interface between human obligation and machine execution. | Translation Layer |
| Control Assertion Engine (CAE) | The infrastructure component that evaluates runtime system behavior against encoded compliance constraints and produces structured assertions describing whether those constraints were satisfied at the moment of execution. | Control Assertion Engine |
| Attestation Layer | The boundary infrastructure system that transforms internal control assertions into externally verifiable evidence artifacts, sitting at the interface between internal operational infrastructure and external oversight processes. | Attestation Layer |
Translation Layer Sub-components
| Term | Definition | First Appears |
|---|---|---|
| Obligation Record | The canonical record created for every obligation entering the Translation Layer, containing source, jurisdiction, effective date, scope, responsible owner, review cadence, and risk classification. Required before an obligation may proceed. | Translation Layer, Stage 1: Obligation Intake |
| Translation Unit | The atomic unit of decomposition produced in semantic decomposition: a normalized obligation broken into its smallest independently assertable component, including intent class, constraint type, subject, object, action, conditions, and ambiguity flags. | Translation Layer, Stage 3: Semantic Decomposition |
| Taxonomy Registry | The versioned registry that maintains the controlled vocabulary used for semantic decomposition of obligations, including version identifiers, change history, term ownership, backward compatibility policy, and retrofit triggers. | Translation Layer, Stage 3 (Ontology Governance) |
| Dependency Replay Process | The process triggered when the Taxonomy Registry changes, requiring re-evaluation of all affected obligations, translation units, control assertions, and evidence bindings to ensure language changes do not silently alter enforcement logic. | Translation Layer, Stage 3 (Ontology Governance) |
| Evidence Binding | A formal specification that ties a control assertion to its evidentiary source, defining the telemetry source, extraction method, schema version, integrity mechanism, validation test, and semantic telemetry checks. | Translation Layer, Stage 5: Evidence Specification and Binding |
| Semantic Telemetry Drift | The condition in which a telemetry field retains its schema name but alters its operational meaning, causing evidence bindings to silently misrepresent system behavior. Detected through distribution analysis, type inference, and classification models. | Translation Layer, Stage 5 (Semantic Telemetry Drift) |
| Traceability Graph | The data structure maintaining bidirectional links across the full compliance evidence chain: Obligation - Translation Unit - Control Assertion - Evidence Binding. Supports weighted edge scoring, cycle detection, and board-level views. | Translation Layer, Stage 6: Traceability Graph Management |
| Translation Drift Report | The artifact produced when a drift trigger (regulatory change, contract change, architecture change, telemetry schema change, etc.) is detected, documenting the impact on the translation chain. | Translation Layer, Stage 7: Drift Detection |
| Conflict Resolution Engine | The Translation Layer component that detects and adjudicates mutually unsatisfiable obligations, using static logic analysis, telemetry collision detection, namespace overlap analysis, and constraint satisfaction failure detection. | Translation Layer, Conflict Resolution Engine |
| Adjudication Record | The machine-readable artifact required for every detected obligation conflict, documenting the conflict class, parties, decision inputs, chosen resolution path, authorized exceptions, and traceability impact. | Translation Layer, Required Artifact: Adjudication Record |
| Boundary Hand-off Protocol | The machine-readable artifact that defines how compliance responsibility is divided between an organization and a third-party provider for a given control assertion, including shared responsibility boundaries, activation requirements, evidence bindings, and anti-false-green rules. | Translation Layer, Required Artifact: Boundary Hand-off Protocol |
| Weighted Sufficiency Scoring | The coverage calculation method that weights evidence by freshness, integrity strength, scope alignment, automation level, and source independence. No inherited control may exceed the attestation weight cap without live operational telemetry. | Translation Layer, Stage 5 (Weighted Sufficiency Scoring) |
Control Assertion Engine Sub-components
| Term | Definition | First Appears |
|---|---|---|
| Control Assertion | A machine-verifiable, formally encoded representation of a compliance requirement expressed as a condition that system behavior must satisfy, together with a structured evaluation result (satisfied, violated, or indeterminate) produced at runtime. | Category Foundation - From Overlay to Inline Enforcement; formally defined in Control Assertion Engine |
| Evidence Pipeline | The processing pipeline that aggregates runtime telemetry from multiple control execution systems, normalizes events into consistent evidence formats, applies cryptographic integrity protections, and manages retention. Transforms raw telemetry into auditable compliance evidence. | Documentation Debt, Section 8 (Evidence Pipelines) |
| Synchronous Evaluation | CAE evaluation mode in which constraint evaluation occurs within the execution path, preventing a system action from completing until the evaluation produces a result. Provides tightest coupling between behavior and assertion; introduces latency into execution paths. | Control Assertion Engine, Evaluation Modes |
| Asynchronous Evaluation | CAE evaluation mode in which events are emitted, captured by the evaluation pipeline, and evaluated on a continuous basis separate from the operational execution path. Introduces assertion lag but removes the CAE from the critical path. | Control Assertion Engine, Evaluation Modes |
| Assertion Object | The atomic unit of compliance evidence produced by the Control Assertion Engine: a structured, machine-generated record containing constraint identifier, event identifier, evaluation result, timestamp, evaluation context, and (where applicable) confidence score. | Control Assertion Engine, Assertion Generation and Evidence Production |
Attestation Layer Sub-components
| Term | Definition | First Appears |
|---|---|---|
| Attestation Artifact | An evidence structure produced from one or more control assertions, packaging the assertion result together with the traceability context required for external verification: regulatory source, constraint definition, enforcement events, and integrity metadata. | Category Foundation - Trust as Verifiable State; formally defined in Attestation Layer |
| Assertion Aggregator | The Attestation Layer component that collects assertion outputs from the Control Assertion Engine, grouping by regulatory domain or control family, correlating assertions addressing overlapping requirements, and enriching context for external reviewers. | Attestation Layer, Internal Architecture |
| Evidence Structuring Engine | The Attestation Layer component that transforms aggregated assertions into interpretable evidence artifacts: control-level summaries, traceable event chains, compliance state timelines, and requirement-linked evidence bundles. | Attestation Layer, Internal Architecture |
| Traceability Index | The structural mapping maintained by the Attestation Layer that connects regulatory requirements to evidence artifacts and supports bidirectional traversal: forward (requirement - evidence) for audit response, and reverse (event - requirements) for incident analysis. | Attestation Layer, Internal Architecture (Traceability Index) |
| Integrity Protection Layer | The Attestation Layer component that applies mechanisms to protect evidence from tampering after production: immutable event logs, cryptographic signatures, secure timestamping, and verifiable evidence chains. | Attestation Layer, Internal Architecture (Integrity Protection Layer) |
| Evidence Integrity | The property that an attestation artifact has not been altered since production. Addressed through the Integrity Protection Layer. Distinct from System Integrity. | Attestation Layer, Integrity and Trust |
| System Integrity | The property that the system producing evidence is operating correctly and has not been compromised. Cannot be guaranteed by evidence integrity mechanisms alone; requires independent infrastructure auditing and separation of concerns. | Attestation Layer, Integrity and Trust |
Trust Anchors
| Term | Definition | First Appears |
|---|---|---|
| Trust Anchor | The mechanism at which a verification chain terminates, supplying the foundational trust that cannot be derived by further computation. Exists in three categories: Cryptographic, Hardware, and Institutional. | Oracle Problem, Section 5 |
| Cryptographic Trust Anchor | A trust anchor grounded in mathematical properties rather than institutional trustworthiness: cryptographic hashes, digital signatures, or zero-knowledge proofs. Oracle boundary is the mathematical primitive. | Oracle Problem, Section 5 (Cryptographic Trust Anchors) |
| Hardware Trust Anchor | A trust anchor grounded in physical execution constraints: trusted execution environments, secure enclaves, TPM chips, and measured boot sequences. Pushes the oracle boundary to the hardware manufacturer and supply chain. | Oracle Problem, Section 5 (Hardware Trust Anchors) |
| Institutional Trust Anchor | A trust anchor supplied by governance mechanisms - independent auditors, regulatory bodies, certification authorities, and legal frameworks - that provides credible assertions backed by professional accountability, legal authority, and organizational consequence. | Oracle Problem, Section 5 (Institutional Trust Anchors) |
Metrics and Diagnostic Signals
| Term | Definition | First Appears |
|---|---|---|
| Assertion Density | The proportion of compliance claims that cannot be derived from internal system state and therefore rely on attestation artifacts. High assertion density indicates high oracle exposure. | Oracle Problem, Section 7 |
| Verification Latency | The delay between control execution and the production of a compliance assertion. High latency increases the window during which system behavior can diverge from the verified state. | Oracle Problem, Section 7 |
| Multi-Oracle Divergence | A signal indicating oracle reliability degradation, detected when independent oracle sources consulted for the same fact produce differing results. | Oracle Problem, Section 7 |
| Weight-Adjusted Translation Coverage | The primary KPI of the Traceability Graph, measuring compliance coverage weighted by the sufficiency score of each evidence binding rather than raw assertion count. | Translation Layer, Stage 6 |