Failure Mechanics
Documentation Debt
How Representational Artifacts Diverge from Operational Reality
1. The Historical Role of Documentation
The Trust Gap section established the conditions under which audit-based compliance verification was designed: stable systems, durable state, and reconstructible records. Documentation flourished in that environment because documentation and system state were synchronized not by design but by circumstance - the pace of change was slow enough that divergence was detectable and correctable before it became significant.
This historical alignment produced a methodological assumption that has persisted long past its validity: that documentation accurately represents operational behavior, and that auditing documentation is therefore equivalent to auditing systems.
That assumption has not held in high-velocity software environments. The conditions that made it approximately true no longer exist.
2. Documentation as Representation
To understand Documentation Debt, it is necessary to be precise about what documentation actually is.
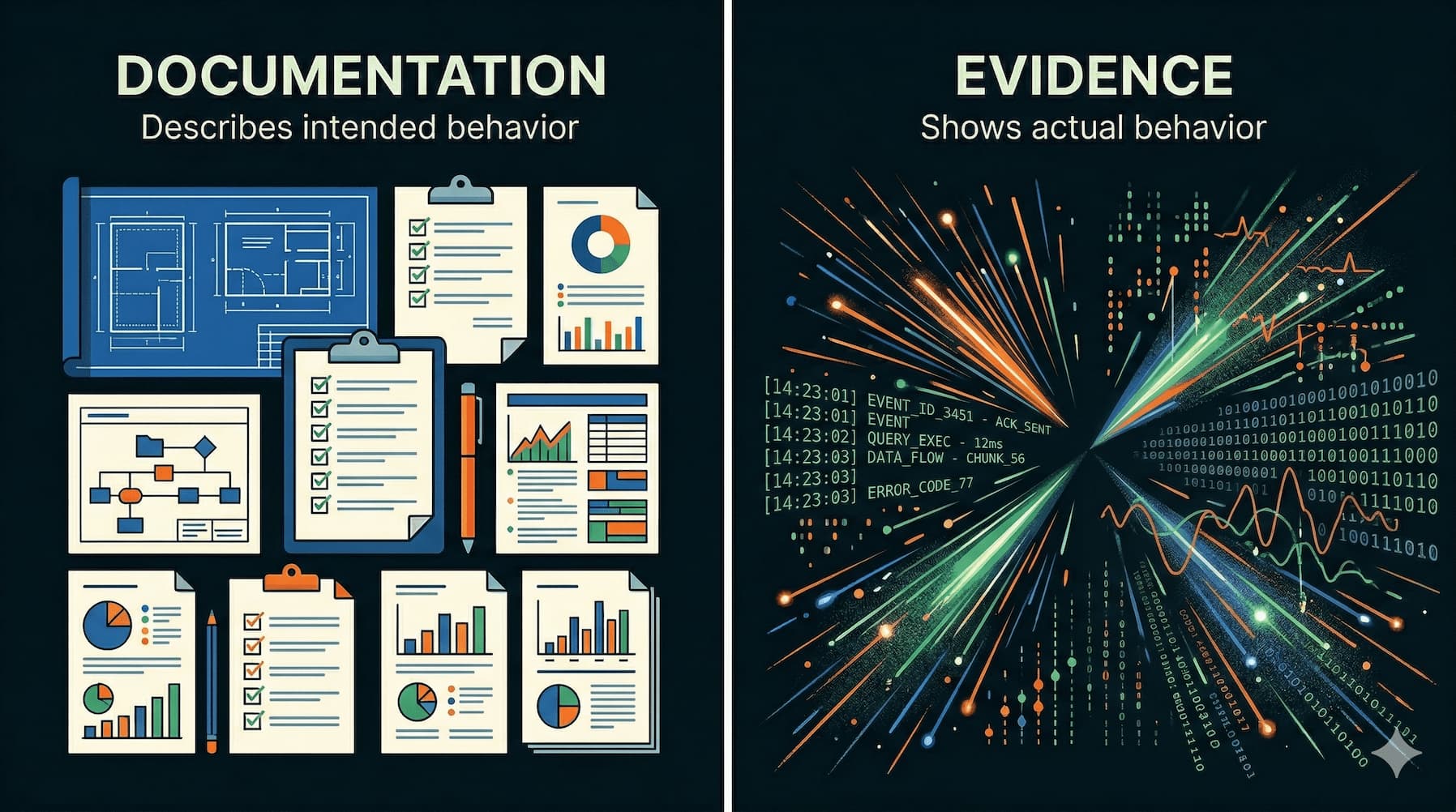
Documentation is a representation of a system - a model constructed by human observers, encoded in human-readable artifacts, intended to describe how a system behaves. It is not the system itself, and it is not a direct observation of system behavior. It is an interpretive layer.
This distinction is structural, not incidental. Documentation operates within a four-layer compliance architecture:
Layer 1 - Control Execution Layer. This is where operational behavior occurs. Infrastructure configuration, deployment pipelines, authentication systems, data access enforcement, and runtime policy enforcement all exist at this layer. System state transitions are produced here. When an access control policy permits or denies a request, that event occurs at the Control Execution Layer.
Layer 2 - Evidence Generation Layer. Systems at this layer capture telemetry produced by control execution. Logs, metrics, audit trails, event streams, and state snapshots are generated here. These artifacts represent observations of control behavior - they record what actually happened at Layer 1. Evidence in traditional systems is observed after the fact. In CAI, evidence is produced at execution.
Layer 3 - Documentation Layer. Human-readable artifacts describe how systems are expected to behave. Policies, procedures, architecture diagrams, control narratives, and runbooks all exist at this layer. These artifacts are models of the system. They describe design intent, operational assumptions, and expected behavior. They do not record actual behavior.
Layer 4 - Audit Observation Layer. External observers - internal auditors, regulators, insurers, certification bodies - evaluate compliance by examining artifacts. In current practice, auditors predominantly examine Layer 3 artifacts. Documentation functions as the primary interface between the operational system and the audit process.
The structural problem is clear: the system contains two sources of truth. Layer 2 captures operational reality through telemetry. Layer 3 describes intended behavior through documentation. These two sources are not inherently synchronized. Documentation Debt is the condition that emerges when they diverge.
The structural problem is clear: the system contains two sources of truth.
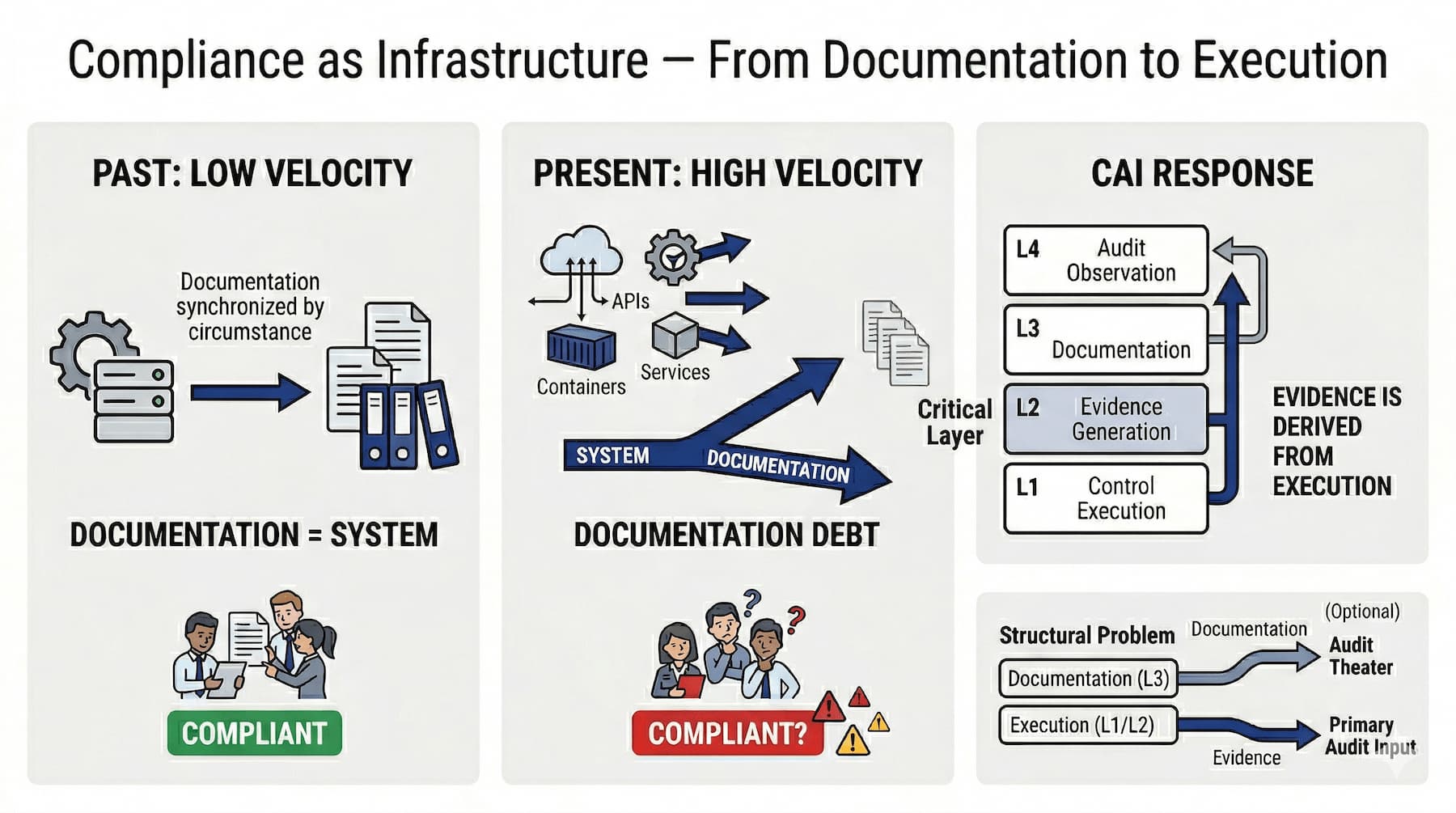
Figure: Documentation and execution diverge under high-velocity conditions, producing Documentation Debt. CAI resolves this by shifting primary evidence from execution rather than representation.
3. The Emergence of Documentation Debt
Documentation Debt is the systematic divergence between descriptive compliance artifacts and the actual behavior of operational systems.
This definition requires precision. Documentation Debt is not the result of carelessness or negligence, though those factors can amplify it. It is the structural consequence of two incompatible properties: documentation evolves episodically, while operational systems evolve continuously.
Documentation Debt accumulates through four interacting mechanisms.
Mechanism 1 - Change Velocity Mismatch. Software systems in continuous delivery environments change frequently. Configuration updates, dependency upgrades, access policy modifications, infrastructure changes, and deployment pipeline alterations occur at rates that can exceed dozens or hundreds of changes per day in mature engineering organizations. Documentation updates occur episodically - during compliance cycles, during incident reviews, during periodic documentation audits, or when personnel identify inaccuracies.
The asymmetry is inherent. System changes are driven by operational requirements. Documentation updates are driven by compliance governance processes. These two drivers operate on different timescales. The result is a systematic lag: operational systems change faster than documentation updates. Every period of normal operation accumulates additional divergence.
Mechanism 2 - Maintenance Cost Scaling. Documentation maintenance cost is not linear. As system complexity increases, the volume of documentation required to describe system behavior grows. More importantly, the number of interdependencies between documented components grows non-linearly. Changing one system component may require updates to architecture diagrams, control narratives, runbooks, policy documents, and procedure descriptions - all of which cross-reference each other.
In organizations operating large microservice architectures, with hundreds of services, thousands of configuration parameters, and frequent deployment events, comprehensive documentation maintenance becomes computationally expensive. Engineering teams face a rational allocation problem: system functionality must be maintained; documentation accuracy competes with that priority and loses systematically.
Organizations do not explicitly decide to accumulate Documentation Debt. They implicitly prioritize system operation over documentation synchronization, because the cost of system failure is immediate and visible, while the cost of documentation divergence is deferred and often invisible until an audit.
Mechanism 3 - Representational Compression. Documentation compresses complex systems into simplified narratives. This compression is necessary - full operational fidelity would produce documentation that is unreadable and unusable. But compression introduces representation error that grows as systems become more dynamic.
Architecture diagrams present static topologies. Modern infrastructure is not static. Ephemeral containers, autoscaling environments, dynamic service meshes, and infrastructure-as-code systems produce infrastructure states that change continuously. A diagram produced during initial deployment may be approximately accurate at the time of production and systematically inaccurate six months later, without any explicit documentation of that change.
Access policy narratives describe expected access control behavior. Dynamic access control systems, attribute-based access control implementations, and just-in-time provisioning systems produce access states that vary based on runtime conditions. A static narrative describing these systems introduces unavoidable representation error.
As systems become more dynamic, static representations become less accurate. The gap between the documentation model and the operational system widens as a function of system dynamism, independent of documentation maintenance effort.
Mechanism 4 - Audit Substitution. Auditors frequently substitute document review for system inspection. This occurs for identifiable reasons: documentation is accessible, it is formatted for human review, it aligns with regulatory expectations for narrative artifacts, and auditors often lack the operational access and technical expertise required to inspect system behavior directly.
The result of audit substitution is a distorted incentive structure. If compliance certification can be obtained through documentation review, organizations are incentivized to maintain documentation that satisfies audit review rather than documentation that accurately represents operational systems. These two objectives can diverge significantly. Documentation optimized for audit review may be coherent, comprehensive, and systematically inaccurate.
Audit substitution does not merely fail to correct Documentation Debt - it actively creates conditions in which Documentation Debt is obscured rather than detected.
4. Observable Signals
Documentation Debt is not directly observable, but it produces measurable signals that indicate the presence and magnitude of divergence.
Signal 1 - Documentation Change Lag. The interval between a system change event and the corresponding documentation update provides a direct measure of representational synchronization. In systems with disciplined documentation maintenance, this interval should be short. In systems accumulating Documentation Debt, this interval extends and becomes inconsistent. Organizations can measure this lag by correlating change management records with documentation version histories.
Signal 2 - Artifact Obsolescence Rate. Systematic review of documentation artifacts reveals the proportion that reference deprecated services, obsolete architectures, or outdated procedures. High obsolescence rates indicate that documentation has decoupled from operational reality. This metric is producible through periodic documentation audits, though those audits themselves consume resources that compete with other compliance activities.
Signal 3 - Audit Evidence Substitution Rate. Tracking the proportion of audit findings satisfied by documentation narratives rather than system telemetry reveals how extensively auditors are substituting documentation for operational evidence. High substitution rates do not indicate compliance - they indicate that compliance assessment has decoupled from operational systems.
Signal 4 - Control Narrative Drift. Control narrative drift is the mismatch between the control behavior described in documentation and the control behavior actually implemented in system configuration. This signal is particularly consequential because it indicates that the compliance controls an organization reports are not the controls actually in operation.
A specific example illustrates the failure mode: policy documentation states that all production access requires multi-factor authentication. The actual runtime configuration of the access control system contains an exception path - a service account, a legacy integration, an emergency access mechanism - that permits access without multi-factor authentication under specific conditions. The documentation is internally consistent and audit-satisfying. The operational system does not implement the described control.
Signal 5 - Runbook Failure Rate. When operational teams execute runbooks during incidents or routine operations and discover that documented procedures do not correspond to actual system behavior, that constitutes an operational signal of Documentation Debt. Runbook failure events - instances where operators deviate from documented procedures because those procedures are inaccurate - represent directly observable evidence of representational divergence.
5. When Documentation Becomes Audit Theater
The convergence of these four accumulation mechanisms and the audit substitution dynamic produces a specific failure condition: audit theater.
Audit theater is the condition in which compliance artifacts satisfy the formal requirements of an audit process while failing to represent the system truth of operational systems. It is not deliberate fraud - it is the structural outcome of applying documentation-based compliance processes to dynamic operational environments.
The mechanics are straightforward. Organizations invest in documentation because documentation satisfies audit requirements. Auditors accept documentation because it satisfies regulatory expectations and because system inspection is technically demanding. Regulatory processes require narrative artifacts because those artifacts were legible before system telemetry was available at scale. Each actor in the compliance ecosystem behaves rationally within its local constraints, and the aggregate result is a compliance assessment process systematically disconnected from operational reality.
The Documentation Debt framing is important here: audit theater is not the result of bad actors. It is the result of applying compliance methodologies developed for static systems to dynamic systems, without updating the methodologies to account for the changed conditions.
The cost of audit theater is not realized during normal operations. It is realized during incidents, regulatory investigations, and enforcement actions - when the gap between documented controls and operational controls becomes consequential.
6. The Visibility Inversion Problem
Documentation Debt produces a specific structural distortion: visibility inversion.
In a correctly functioning compliance architecture, audit observation should reflect operational reality. Auditors should be able to determine whether operational controls are functioning correctly. The compliance assessment process should be sensitive to actual control failure.
In a documentation-based compliance architecture with accumulated Documentation Debt, this relationship inverts. Auditors observe documentation - which describes intended design. The operational system executes actual behavior. Auditors evaluate intent, not execution.
Visibility inversion means that a system can satisfy audit review while experiencing significant control failures, provided the documentation accurately describes intended controls rather than operational controls. Conversely, a system that has implemented controls differently than documented - even if the implemented controls are functionally superior - may fail audit review because documentation and operation have diverged.
This inversion is not a pathological edge case. It is the predictable consequence of documentation-based compliance in environments where system dynamism exceeds documentation maintenance capacity. As system complexity and deployment velocity increase, visibility inversion becomes the default condition rather than the exception.
7. Documentation Is Not the Enemy
Before proceeding to architectural responses, a necessary clarification: Documentation Debt is not an argument against documentation.
Documentation serves legitimate and non-substitutable functions within compliance architecture.
Interpretation. Documentation provides the semantic context required to interpret operational evidence. Telemetry records that a configuration change occurred. Documentation explains what that change was intended to accomplish and what compliance implications it carries. Observability systems without interpretive documentation produce evidence without meaning.
Coordination. Documentation enables organizational coordination across engineering, compliance, legal, and risk functions. Shared understanding of system behavior, control design, and compliance obligations requires human-readable artifacts. Machine-verifiable control assertions cannot replace this coordination function.
Legal Risk Transfer. Documentation creates auditable records of governance decisions, control design rationale, and risk acceptance. These artifacts serve legal functions in regulatory proceedings and litigation that operational telemetry alone cannot fulfill.
The argument of this chapter is precisely bounded: documentation cannot function as the primary evidence mechanism in high-velocity software environments. Its legitimate roles - interpretation, coordination, legal risk transfer - do not include serving as the primary basis for compliance verification. When documentation is used as primary evidence, the result is compliance assessment systematically detached from operational behavior.
The architectural implication is a shift in function, not elimination. Documentation remains necessary. It is reassigned from evidence production to interpretation and governance.
8. Infrastructure Requires Operational Evidence
The structural response to Documentation Debt is an architectural shift in the evidence layer: moving from documentation-as-evidence to system-telemetry-as-evidence.
This shift requires specific infrastructure components.
Runtime Evidence Generation. Systems must generate machine-verifiable records of control execution at the point of execution. Policy enforcement events, configuration state snapshots, access control decisions, and system state transitions must be captured as structured, integrity-protected records at Layer 2. These records constitute primary compliance evidence.
This requirement has architectural implications. Systems must be designed to emit compliance-relevant telemetry as a function of normal operation, not as a post-hoc reporting activity. Evidence generation cannot be separated from control execution - if evidence is generated separately, it reintroduces the synchronization problem that documentation-based compliance exhibits.
Control Assertion Engine. Controls must be expressed as verifiable assertions about system state, not as prose descriptions of intended behavior. The difference is operationally consequential.
A prose control description states: "All production access requires multi-factor authentication." This description can be documented, audited against documentation, and certified - without any verification that the operational system actually enforces the described control.
A control assertion expresses the same requirement in machine-verifiable form:
∀ user: ProductionAccess(user) ⇒ MFAEnabled(user)
This assertion can be evaluated against the operational control plane continuously. Violations produce evidence of control failure at the time of failure, not at the time of the next audit cycle. The assertion is either satisfied or it is not, and that evaluation is not contingent on documentation accuracy.
Control assertions shift compliance verification from documentation review to system state verification - from observation of intent to observation of execution.
Evidence Pipelines. Runtime telemetry must be transformed into structured compliance evidence through defined processing pipelines. Raw telemetry is not directly auditable - it requires aggregation, normalization, integrity protection, and retention management before it constitutes usable compliance evidence.
Evidence pipelines perform this transformation. They aggregate events from multiple control execution systems, normalize them into consistent evidence formats, apply cryptographic integrity protections, and manage retention in accordance with regulatory requirements. The output of evidence pipelines constitutes the attestation artifact set that replaces documentation as the primary audit input.
Attestation Systems. Attestation systems produce cryptographically verifiable records of control state at defined points in time. These attestation artifacts become the primary audit artifact. Unlike documentation, attestation artifacts record what the system actually did, not what it was intended to do. Unlike raw telemetry, attestation artifacts are structured for human and machine review.
Attestation artifacts must be designed to satisfy the evidentiary requirements of audit processes while grounding those processes in operational reality rather than documentation.
9. Preparing the Infrastructure Solution
This section establishes the diagnostic boundary for the architecture that follows.
Documentation emerged as a proxy for operational observation in low-velocity environments where the proxy was approximately accurate. That approximation depended on conditions that no longer exist. In high-velocity software systems, documentation and system state diverge as a matter of normal operation, not as a matter of discipline.
Documentation Debt accumulates through structural mechanisms: change velocity mismatch, maintenance cost scaling, representational compression, and audit substitution. These mechanisms are not correctable through improved process, increased rigor, or stricter documentation standards. They are properties of the system.
The result is visibility inversion. Compliance processes observe intent rather than execution. Audit certification becomes structurally decoupled from operational control state. Systems can pass audit while controls fail, and fail audit while controls function. The relationship between assessment and reality is inverted.
This is the boundary condition. Documentation cannot serve as the primary evidence layer in environments where operational state changes continuously.
The architectural response is not incremental. It is a reassignment of the evidence function.
Primary evidence moves to the point of control execution. Systems generate machine-verifiable telemetry as a function of operation. Controls are expressed as assertions over system state. Evidence is produced, processed, and attested through infrastructure that observes execution directly.
Documentation remains. Its role changes. It provides interpretation, coordination, and legal record. It no longer functions as evidence.
Documentation Debt is not a documentation problem. It is an evidence architecture problem.
As long as evidence is derived from representation, divergence is unavoidable.
When evidence is derived from execution, the representational layer can no longer introduce divergence into the compliance system.