Category Foundation
This section establishes the conceptual foundation of the compliance as infrastructure category. It explains why the traditional compliance model is failing, why a new category is emerging, how the category is defined, and what its long-term trajectory implies for modern digital systems.
The goal of this section is not to describe a specific implementation, but to establish the structural shift in governance architecture that makes the category necessary.

Why This Category Matters Now
The Failure of the Point-in-Time Model
For decades, compliance has operated as a point-in-time exercise.
Organizations assemble documentation. Controls are reviewed. Evidence is sampled. An audit report is issued. The system is declared compliant at a specific moment.
This model assumes that system behavior is relatively stable between verification cycles.
Modern digital systems no longer behave in moments.
Infrastructure scales dynamically. Software deploys continuously. Integrations evolve without notice. Artificial intelligence systems update through retraining and configuration changes.
When system behavior becomes continuous, compliance cannot remain episodic.
The central structural tension is simple: periodic proof attempts to evaluate systems that no longer exist in discrete states.
Compliance as infrastructure resolves this tension by treating compliance as a continuously observable system state rather than a periodically declared status.
From Overlay to Inline Enforcement
Most modern compliance tooling still operates as an overlay.
Logs are collected. Evidence is aggregated. Dashboards are assembled after systems have already executed.
These tools observe behavior but do not shape it.
Infrastructure operates differently. Infrastructure sits directly in the execution path. Compliance as infrastructure moves regulatory and contractual constraints into the same layers that control system deployment, access, and configuration.
In this model:
- Policies are translated into executable control assertions
- Control assertions are enforced inline within production workflows
- Telemetry is generated as a byproduct of execution
- Attestation reflects actual system state rather than retrospective documentation
The architectural shift is mechanical, not rhetorical. If disabling compliance controls does not alter production behavior, compliance is still operating as an overlay.
Continuous Change Requires Continuous State
Digital systems now operate as continuously evolving environments. Deployment cycles shorten. Infrastructure becomes programmable. Systems rely on distributed services and automated decision layers.
A periodic audit cannot meaningfully capture a continuously mutating system.
Compliance as infrastructure reframes compliance as a state machine:
- Controls have defined states
- Enforcement drift is measurable
- Evidence latency becomes observable
- Deviations become detectable in near real time
Traditional compliance language does not include these concepts because its tools were designed for periodic verification. As system velocity increases, continuous state validation becomes structurally necessary.
The Emergence of a Category
Categories Form When Prior Models Break
New categories do not emerge because someone invents a term. They emerge when an existing model can no longer absorb the operational demands placed upon it.
For decades, compliance operated as a perimeter function. Policies were defined externally to systems. Evidence was gathered periodically. Auditors validated documentation. Engineering implemented controls but did not own compliance architecture.
That model assumed:
- Systems changed slowly
- Infrastructure was relatively static
- Risk could be sampled at intervals
- Human review served as the primary assurance mechanism
Modern digital environments violate these assumptions. When the underlying assumptions collapse, the governance model must evolve.
Structural Forces Driving the Shift
Three structural forces drive the emergence of this category.
Ephemeral Infrastructure. Cloud-native systems scale dynamically. Resources may exist for minutes rather than years. Snapshot audits cannot meaningfully capture transient system state.
Continuous Deployment. Software now changes weekly or daily. Control configurations evolve alongside code. Periodic verification increasingly lags behind operational reality.
Automated and Probabilistic Systems. Decision logic increasingly resides in automated workflows and AI-driven systems. Risk exposure moves from static documentation into execution pathways.
These forces do not simply increase compliance workload. They undermine the architecture of point-in-time assurance.
From Department to Platform
Earlier movements such as DevSecOps and GRC automation integrated governance processes into development workflows. Compliance as infrastructure extends this shift further.
It moves compliance from a departmental coordination function to a platform-level enforcement layer.
In the traditional model, compliance checks systems. In the infrastructure model, systems enforce compliance.
Policy requirements become control assertions. Enforcement resides within orchestration layers. Telemetry becomes an inherent property of execution. Compliance ceases to be an external evaluation and becomes a system constraint.
Category Boundaries and Tests
Defining the Category
Identifying the failure of the existing model does not automatically define a new one. A category earns legitimacy when its boundaries can be described precisely.
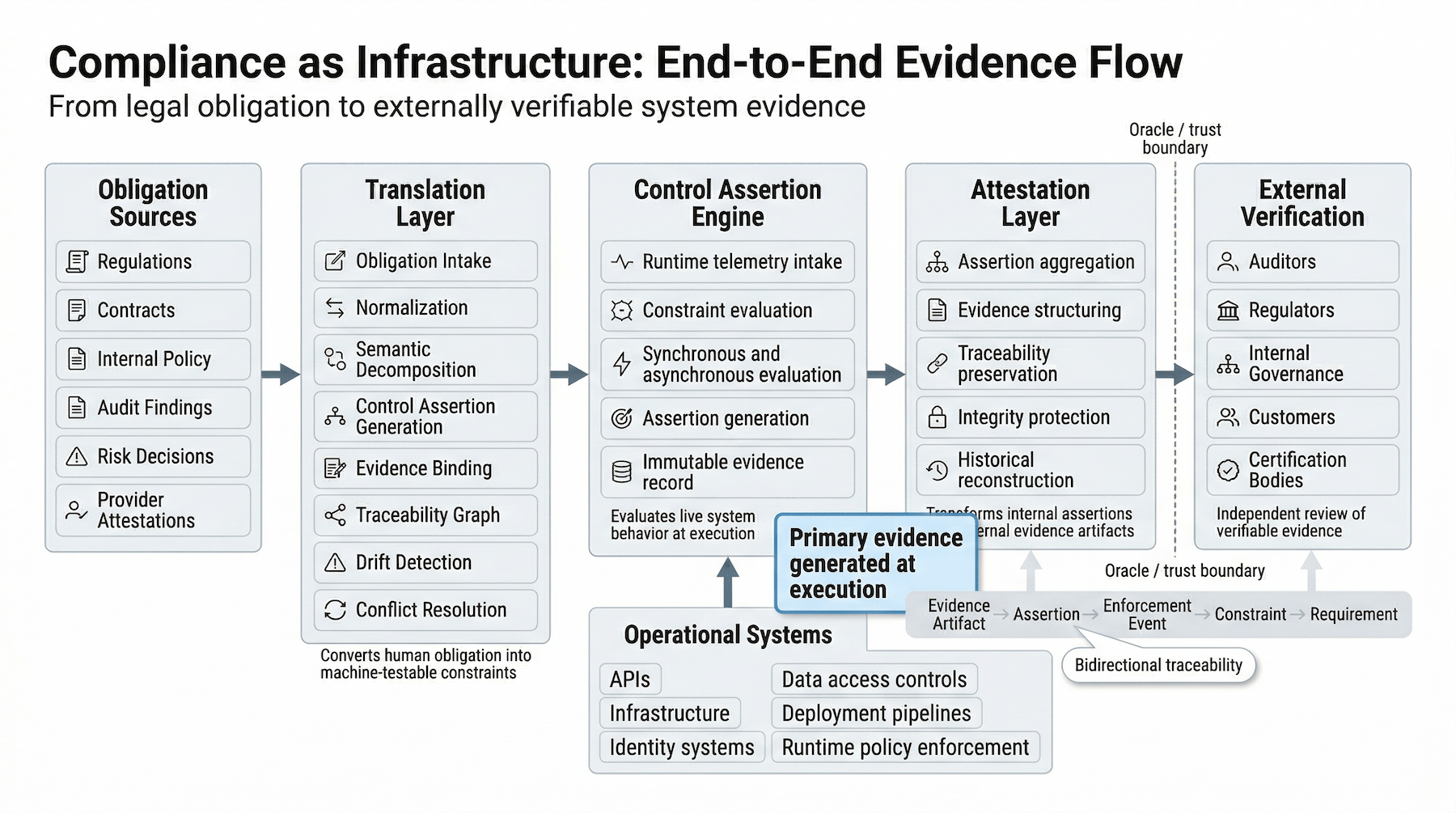
Compliance as infrastructure is defined as the embedding of regulatory and contractual constraints directly into the execution and orchestration layers of production systems.
In this model:
- Policy requirements become executable control assertions
- Control assertions are enforced inline within production workflows
- Telemetry emerges from system execution rather than retrospective assembly
- Evidence derives from observable system state
Compliance becomes a continuously evaluated property of the system itself.
Boundary Tests
The following architectural tests distinguish infrastructure-based compliance from monitoring or automation overlays.
Disable Without Consequence Test. If compliance controls can be disabled without altering production behavior, compliance is operating as an overlay rather than infrastructure.
Post-Execution Test. If evidence is generated only after system execution through log aggregation or manual reconstruction, compliance remains observational rather than embedded.
Point-in-Time Dependence Test. If the system cannot describe its current compliance state without reconstructing historical documentation, it remains dependent on periodic proof.
Human-Only Validation Test. If regulatory conformity depends entirely on manual review rather than machine-verifiable control assertions, infrastructure embedding has not occurred.
These tests are architectural rather than rhetorical. They distinguish continuous monitoring from structural integration.
Monitoring Is Not Infrastructure
Many systems marketed as "continuous compliance" automate evidence collection. Automation reduces manual effort but does not alter the locus of enforcement.
Monitoring observes system behavior. Infrastructure shapes system behavior.
Compliance as infrastructure places constraint directly in the execution path of digital systems.
The Long-Term Vision
From Concept to Baseline
Major architectural shifts eventually become invisible. Cloud computing moved from innovation to expectation. Continuous integration moved from experiment to baseline practice. Security evolved from optional feature to operational necessity.
Compliance as infrastructure follows the same trajectory.
The long-term vision is not rhetorical ambition. It is a structural claim: regulatory constraints become a persistent control layer within operational systems. When compliance behaves as infrastructure, it becomes versioned, observable, testable, and continuously enforced.
Trust as Verifiable State
Trust in this model does not rely on declarations. It emerges from verifiable system state.
This includes:
- Continuous control enforcement
- Observable telemetry streams
- Cryptographically anchored attestation artifacts
- Tamper-evident logging
Auditors do not disappear. Their role evolves. Rather than sampling documentation, auditors evaluate the integrity of the control plane, the validity of telemetry streams, the reliability of attestation mechanisms, and evidence latency and enforcement drift.
Trust shifts from periodic review toward continuous system validation.
Economic Reallocation
Embedding compliance into infrastructure increases upfront engineering cost. Control planes must be designed. Telemetry must be hardened. Constraint lifecycles must be managed.
However, the economic structure changes. Traditional compliance scales linearly with organizational growth. More systems require more audits, more evidence collection, and more reconciliation. Infrastructure-based compliance shifts the cost curve toward fixed architectural investment with declining marginal verification cost.
Friction does not disappear. It moves earlier in the system lifecycle, where it is cheaper and more predictable.
Beyond the Single Organization
The long-term vision also depends on interoperability. Organizations can expose standardized attestation artifacts, compatible control schemas, and machine-readable evidence formats.
When these elements align, external validation becomes more efficient. Trust across organizational ecosystems improves only when:
- Control assertions are defined consistently
- Evidence formats are interoperable
- Attestation integrity can be independently verified
Absent these conditions, the compliance as infrastructure model collapses back into fragmented verification processes.
The Direction of Travel
Compliance as infrastructure describes a shift in organizational architecture. It does not eliminate auditors. It does not remove liability. It does not promise frictionless governance.
Instead, it relocates compliance enforcement from external review into the control plane of operational systems.
As digital systems grow more complex and regulatory expectations increase, embedding constraint into infrastructure becomes a structural response rather than an optional design choice. The category emerges not because it is fashionable, but because the existing model becomes increasingly unstable under modern system dynamics.
Category Foundation has defined the category and its structural logic. Trust Gap examines the specific failure condition that makes the category necessary — and demonstrates why that condition cannot be resolved by refinements to existing compliance practice.