Attestation Layer
From Internal Assertion to External Evidence
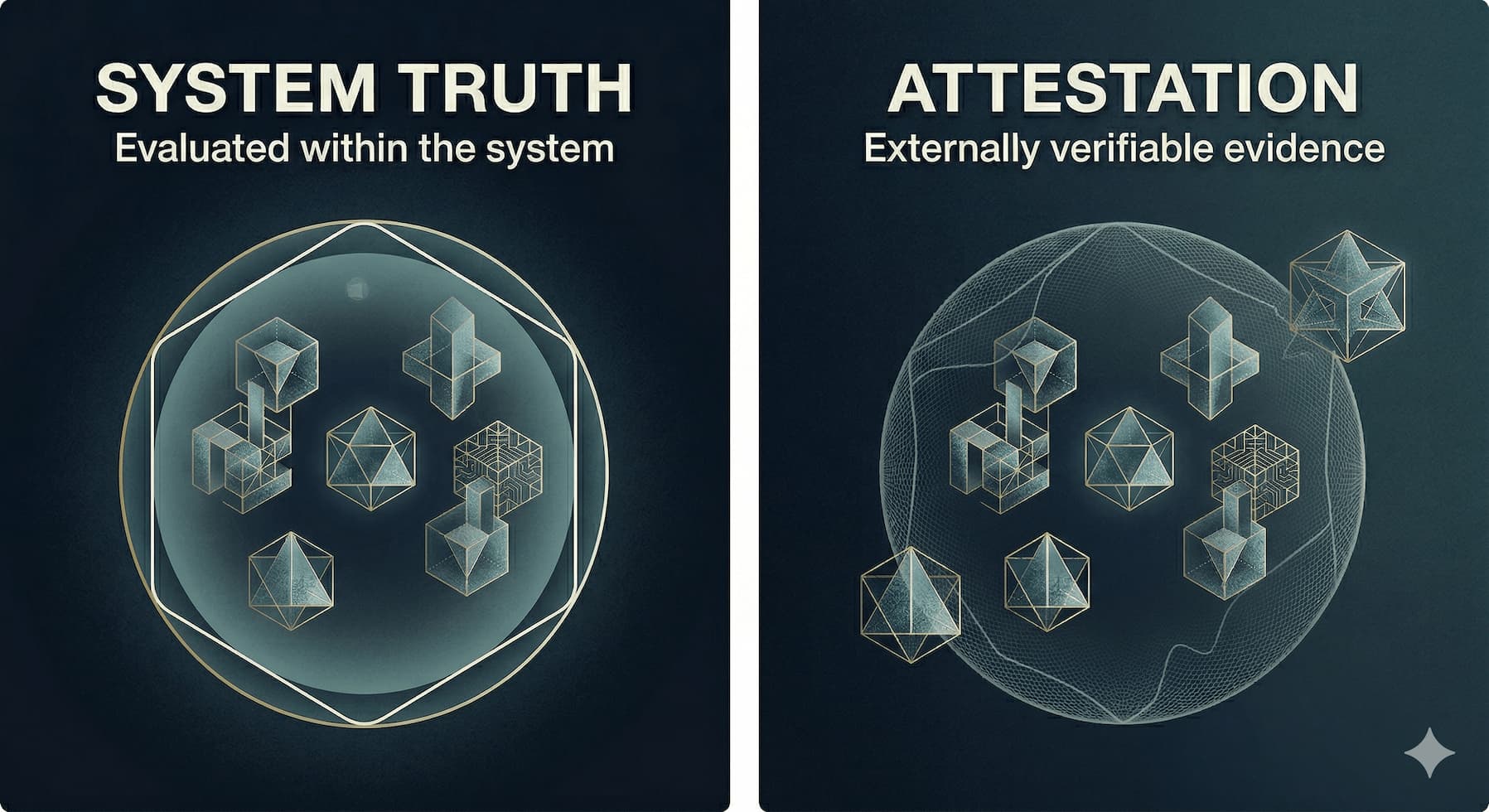
Compliance systems generate two distinct categories of output. The first is internal: assertions produced by infrastructure systems evaluating their own behavior against defined constraints. The second is external: evidence artifacts that allow independent parties to inspect, challenge, and evaluate those assertions. Most organizations treat these categories as equivalent. They are not.
An assertion is a system statement. An attestation artifact is a verifiable evidence structure. The gap between them is not semantic. It is architectural. Without a structured mechanism to transform internal assertions into externally consumable evidence, compliance becomes a documentation exercise rather than a systems property. This section defines the Attestation Layer - the infrastructure boundary system that bridges operational assertion and external verification.
The Compliance Evidence Problem
Traditional compliance processes produce evidence through retrospective assembly. When an audit occurs, compliance teams locate logs, extract documentation, construct narratives, and present assembled artifacts to external reviewers. This process has structural deficiencies that are independent of how diligently teams execute it.
Evidence produced through retrospective assembly is fragmented by design. Logs exist in operational systems. Policy enforcement records exist in control systems. Configuration states are captured episodically. The linkage between a regulatory requirement and a specific system behavior event is rarely preserved as a first-class artifact. Instead, it is reconstructed at audit time through human interpretation of disparate data sources.
This produces four compounding failure modes.
Evidence Fragmentation. Compliance assertions are distributed across logs, screenshots, manual reports, and documentation artifacts. No durable structural linkage connects system behavior to the compliance claims derived from it. Each audit requires reconstruction of connections that should have been preserved at the time of the underlying event.
Audit Reconstruction Overhead. Because evidence is not continuously organized, preparation becomes a parallel operational process. Teams assemble evidence bundles, create retrospective narratives, and produce artifacts specifically for audit consumption rather than deriving audit artifacts from operational records. This overhead scales with audit frequency and scope.
Evidence Latency. The delay between a system behavior event and the production of a compliance-relevant evidence artifact increases the distance between operational truth and verifiable record. When that delay is measured in days or weeks, enforcement drift accumulates. Conditions that existed at the time of a behavior are not accurately captured in evidence produced long afterward.
Trust Gaps. External reviewers operating on retrospectively assembled evidence cannot directly inspect operational system behavior. They inspect documentation about that behavior. The evidentiary chain runs through human interpretation at multiple points, each of which introduces variance, selection effects, and the possibility of inadvertent or deliberate distortion.
The cumulative result is a compliance model that produces narrative verification rather than system verification. Regulators and auditors evaluate descriptions of system behavior. The Attestation Layer is the architectural mechanism that makes system behavior itself the evidence.
From Assertion to Attestation
The distinction between assertion and attestation requires precise definition, because conflating them produces architectural errors that manifest as governance failures.
A control assertion is a machine-generated evaluation result. It answers the question: does this system's current behavior satisfy this constraint? The assertion is produced by the Control Assertion Engine, which evaluates observable system state against the constraint definitions encoded in the control plane. An assertion is an internal artifact. It is meaningful within the operational system, but it is not, by itself, externally verifiable.
An attestation artifact is an evidence structure produced from one or more assertions. It packages the assertion result together with the traceability context required for external verification: the regulatory requirement that generated the constraint, the constraint definition itself, the enforcement events that produced the assertion, and the integrity metadata that allows a reviewer to confirm the artifact has not been altered. An attestation artifact is interpretable by parties outside the operational system without requiring access to that system's internals.
The transformation from assertion to attestation artifact is not a formatting operation. It requires structural enrichment. The raw assertion must be linked to its upstream regulatory source. The underlying enforcement events must be preserved and attached. The temporal context must be captured. Integrity protection must be applied. Only after this transformation does the artifact become externally useful evidence.
The Attestation Layer is the infrastructure that performs this transformation continuously, at scale, and in a form that preserves verifiability over time.
The Attestation Layer: Architectural Definition
The Attestation Layer is a boundary system. It sits at the interface between internal operational infrastructure and external oversight processes. It does not generate compliance determinations. It exposes verifiable system behavior to the verification processes of external actors - regulators, auditors, internal governance bodies, customers, and certification entities.
The layer performs three defined functions.
Evidence Packaging. The Attestation Layer receives assertion outputs from the Control Assertion Engine and organizes them into structured evidence artifacts. Packaging is not summarization. A summary discards information. Evidence packaging preserves the full traceability context of each assertion while organizing it into a form accessible to external reviewers without requiring operational system access.
Traceability Preservation. The layer maintains bidirectional linkage across the full compliance evidence chain:
Regulatory Requirement ↓ Constraint Definition ↓ System Enforcement Event ↓ Generated Assertion ↓ Evidence Artifact
This linkage is the architectural property that distinguishes infrastructure-generated evidence from documentation-based evidence. A reviewer can traverse from a regulatory requirement to the specific system events that produced a compliance assertion, without interpolation or retrospective construction.
Verification Enablement. The layer exposes evidence through interfaces that allow external actors to inspect evidence, validate event traces, verify claims against underlying records, and reconstruct historical compliance state. Verification enablement is not passive disclosure. It requires the Attestation Layer to maintain evidence in a queryable, interpretable form across time horizons relevant to regulatory and audit processes.
Internal Architecture
The Attestation Layer comprises four functional components.
Assertion Aggregator
The Assertion Aggregator collects assertion outputs from the Control Assertion Engine across the operational system. Its functions are grouping, correlation, and context enrichment.
Grouping organizes assertions by regulatory domain, control family, or system boundary. Correlation links assertions that address overlapping regulatory requirements or that derive from shared enforcement events. Context enrichment attaches operational metadata - system identifiers, timestamp records, constraint version references - that external reviewers require to evaluate evidence meaningfully.
The Aggregator is the intake point of the evidence pipeline. Its performance characteristics directly affect the freshness and completeness of attestation artifacts.
Evidence Structuring Engine
The Evidence Structuring Engine transforms aggregated assertions into interpretable evidence artifacts. The transformation produces several artifact types:
- Control-level summaries: consolidated records of a control's enforcement history across a defined period
- Traceable event chains: sequential records of the enforcement events that produced a specific assertion
- Compliance state timelines: temporal views of system compliance posture, enabling point-in-time reconstruction
- Requirement-linked evidence bundles: artifact sets organized by the regulatory requirement they address
The structuring operation must preserve sufficient information for each artifact to stand independently as evidence. An auditor reviewing a requirement-linked evidence bundle should be able to evaluate the underlying enforcement events without requiring access to the operational system that produced them.
Traceability Index
The Traceability Index maintains the structural mapping that connects regulatory requirements to evidence artifacts. It is the mechanism that makes bidirectional traversal of the evidence chain possible.
Architecturally, the index must support two query patterns. The forward query begins at a regulatory requirement and produces the evidence artifacts that demonstrate compliance with that requirement. The reverse query begins at a system event or enforcement action and identifies the regulatory requirements it addresses and the assertions it contributed to.
Both query patterns are essential. Forward queries support audit response. Reverse queries support incident analysis - specifically, when a system behavior change occurs, identifying which compliance assertions are affected and which evidence artifacts require revalidation.
Integrity Protection Layer
The Integrity Protection Layer applies mechanisms that protect evidence from tampering after production. The requirement for integrity protection derives from the evidentiary function of the artifacts themselves. Evidence that can be altered without detection is not evidence. It is a document.
Mechanisms include:
- Immutable event logs: append-only storage architectures that prevent modification of existing records
- Cryptographic signatures: applied to evidence artifacts at production time, enabling verification that artifact content has not changed since signing
- Secure timestamping: third-party or infrastructure-provided timestamps that establish the production time of an artifact independently of the producing system's clock
- Verifiable evidence chains: hash-linked artifact sequences that allow detection of any gap or alteration in the evidence record
The specific mechanisms appropriate to a given architecture depend on the threat model and the regulatory expectations of the relevant oversight bodies. The principle is uniform: evidence integrity must be verifiable by parties who do not trust the producing system.
Evidence Structuring in Practice
The transformation from raw assertion to structured evidence artifact is the operational core of the Attestation Layer. Understanding its mechanics is necessary to evaluate whether a specific implementation is architecturally sound.
A raw assertion might state: control C-47 evaluated system S at time T against constraint K and produced result COMPLIANT. This is operationally useful but externally insufficient. An external reviewer cannot verify the assertion without knowing what constraint K encodes, what regulatory requirement generated it, what enforcement events occurred at time T, and whether the assertion result accurately reflects those events.
A structured evidence artifact for the same assertion includes:
- The regulatory requirement that generated constraint K, with version reference
- The constraint definition K in its current version
- The enforcement events from system S at time T that the Control Assertion Engine evaluated
- The assertion logic applied to those events
- The assertion result, with production timestamp and signing metadata
- The Traceability Index reference linking the artifact to its position in the evidence chain
This artifact can be evaluated by an external reviewer without access to system S, without access to the Control Assertion Engine, and without reconstruction from memory or documentation. It is self-contained evidence.
The cost of this completeness is storage and pipeline throughput. Evidence pipelines that produce artifacts at this fidelity generate significant data volumes. Evidence storage architecture must be designed accordingly: append-only, durable, high-integrity, and capable of supporting query interfaces at the volume levels generated by continuous attestation.
Traceability and Evidence Chains
Traceability is the property that allows a reviewer to determine, for any compliance assertion, the complete chain of causation from regulatory requirement to evidence artifact. It is not a documentation property. It is a structural property of the evidence system.
The Traceability Index must maintain this chain without gaps. A gap in the chain - a missing link between a system enforcement event and the assertion it contributed to, or between a constraint and the regulatory requirement it encodes - produces a traceability break. A traceability break is a failure of the Attestation Layer, not merely an evidence quality issue. It means that a portion of the compliance posture cannot be externally verified.
Traceability failures manifest in predictable patterns. Evidence drift occurs when evidence artifacts cannot be connected to the operational events they purport to represent. This happens when logging gaps, assertion aggregation failures, or index corruption sever links in the chain. Documentation reversion occurs when organizations, unable to produce traceable machine-generated evidence, fall back to exporting operational data into static reports and presenting those reports as compliance evidence. This is operationally identical to the fragmented evidence model the Attestation Layer is designed to replace. Verification ambiguity occurs when external reviewers cannot determine the provenance or integrity of evidence artifacts - they cannot establish where the evidence originated or whether it was modified after production.
Maintaining traceability requires active infrastructure management. The Traceability Index must be updated continuously as new assertions are produced. Evidence artifacts must be linked at production time, not retroactively. Integrity mechanisms must be applied before artifacts enter storage. These are pipeline requirements, not post-processing requirements.
Integrity and Trust
The credibility of infrastructure-generated evidence depends entirely on the integrity of the systems that produce it. This creates a recursive problem: the Attestation Layer must itself be trustworthy, but it is an infrastructure system subject to the same failure modes and adversarial pressures as any other infrastructure component.
Two integrity requirements are distinct and must be addressed separately.
Evidence integrity is the property that an artifact has not been altered since production. This is addressed through the Integrity Protection Layer mechanisms described above. Cryptographic signatures, immutable storage, and verifiable chains allow a reviewer to confirm that an artifact's content matches what the system produced.
System integrity is the property that the system producing evidence is operating correctly and has not been compromised. Evidence integrity mechanisms cannot address system integrity failures. A compromised assertion engine that produces false assertions will produce cryptographically valid evidence artifacts for those false assertions. The integrity protection mechanisms will confirm that the artifacts have not been altered - which is accurate, but not sufficient to detect the upstream falsification.
Addressing system integrity requires mechanisms that extend beyond the Attestation Layer itself:
- Independent infrastructure auditing: the Attestation Layer must produce evidence of its own operation, enabling external parties to verify that the layer is functioning as specified
- Separation of concerns: the systems that produce assertions and the systems that protect evidence integrity must be architecturally separated, so that compromise of one does not automatically compromise the other
- Attestation of attestation infrastructure: in high-integrity environments, the infrastructure supporting the Attestation Layer - storage systems, signing infrastructure, index systems - may itself require formal attestation
The principle that the Attestation Layer must produce evidence of its own operation is not recursive decoration. It is an architectural necessity. An oversight body evaluating infrastructure-generated evidence must be able to confirm that the infrastructure generating that evidence was operating within specification.
Interaction With Auditors and Regulators
External verification actors - auditors, regulators, internal governance bodies, customers, certification bodies - interact with the Attestation Layer through verification interfaces. These interfaces must support specific operational patterns.
Evidence inspection allows a reviewer to examine specific attestation artifacts. The interface must present artifacts in a form interpretable without specialized system knowledge - the artifact must carry sufficient context to be self-explanatory to a reviewer with domain knowledge but without operational system access.
Event trace validation allows a reviewer to follow the enforcement event chain that produced a specific assertion. The reviewer can confirm that the events described in the evidence artifact match the records in the event log, and that the assertion result is consistent with those events.
Claim verification allows a reviewer to validate specific compliance claims against underlying evidence. The interface must support targeted queries - given this regulatory requirement, what evidence exists that this system satisfies it, and what is the evidence's provenance?
Historical compliance reconstruction allows a reviewer to determine compliance posture at a specific point in time. This is particularly important for incident analysis and regulatory investigations, where the relevant question is not the current compliance state but the state at a specific past moment.
These capabilities require the Attestation Layer to maintain evidence in a form that supports temporal queries. Evidence stored only as current-state snapshots does not support historical reconstruction. The storage architecture must preserve the full event history, not just current-state records.
The interaction model also has organizational implications. When external reviewers have direct query access to attestation artifacts, the audit process changes structurally. Evidence preparation time decreases because evidence is retrieved rather than assembled. Evidence fidelity increases because the artifacts are produced by operational systems rather than reconstructed by compliance teams. Reviewer confidence in evidence provenance increases because traceability chains are directly inspectable rather than asserted in documentation.
Limits of Infrastructure Attestation
The Attestation Layer exposes technical truth. It does not produce legal truth. This distinction is foundational, and its implications must be explicitly acknowledged in any compliance architecture that incorporates infrastructure-generated evidence.
Technical truth versus legal truth. A compliance assertion states that a system behavior satisfies a defined constraint. Whether that constraint correctly encodes the applicable regulatory requirement, and whether satisfying the constraint constitutes legal compliance, are questions of legal and regulatory interpretation. These questions are answered by human processes - legal analysis, regulatory guidance, judicial interpretation - not by infrastructure systems. The Attestation Layer provides the evidentiary basis for that interpretation. It does not perform the interpretation.
This means that infrastructure attestation can demonstrate that a system did what its constraints required. It cannot demonstrate that the constraints required the right thing. Constraint definition is the upstream process that determines whether the compliance architecture addresses the actual regulatory obligation. The Attestation Layer's evidence is only as meaningful as the constraints it evaluates against.
The oracle problem. Infrastructure systems can only attest to events within their observational scope. Business processes, human decisions, third-party activities, and off-system operations that are relevant to regulatory compliance exist outside the system boundary. The Attestation Layer cannot produce evidence about events it cannot observe. Organizations must maintain explicit awareness of the boundary between what their attestation infrastructure covers and what it does not.
This boundary is a compliance risk. Regulatory obligations do not constrain themselves to system-observable events. An organization that presents infrastructure-generated evidence as comprehensive compliance evidence without acknowledging what falls outside system observability is misrepresenting its evidence.
Regulatory acceptance. Infrastructure-generated evidence is a relatively recent phenomenon in regulatory practice. The degree to which specific oversight bodies accept, require, or discount such evidence varies by jurisdiction, regulatory domain, and the maturity of the oversight body's technical capacity. Attestation infrastructure should be designed with awareness of the verification methods and evidence standards applied by the specific regulatory bodies that will evaluate the evidence.
In some contexts, machine-generated evidence with full traceability and cryptographic integrity may be more persuasive than traditional documentation. In others, regulators may require human attestation - an authorized individual vouching for the accuracy of a compliance claim - in addition to or instead of system-generated evidence. The Attestation Layer architecture must accommodate the actual evidence standards of the relevant regulatory environment, not an idealized model of what those standards should be.
Architectural Risks
Three architectural risks are specific to attestation infrastructure and require deliberate design mitigation.
Compromised evidence systems. The Attestation Layer is a high-value target for any actor seeking to conceal compliance failures. If the evidence system can be compromised, false attestation artifacts become possible. Mitigation requires architectural separation between operational systems and evidence systems, strong access controls on evidence infrastructure, integrity monitoring of the attestation pipeline itself, and the attestation-of-attestation mechanisms described above.
Adversarial optimization. When organizations know the specific assertions their attestation infrastructure evaluates, they may optimize behavior to satisfy those assertions without addressing the underlying regulatory intent. A system optimized to produce compliant assertions rather than compliant behavior will generate attestation artifacts that accurately reflect its assertion results while those results fail to capture actual regulatory risk. This is a constraint definition problem with manifestation in the attestation layer. It requires the constraint lifecycle - the upstream process that defines what the Control Assertion Engine evaluates - to maintain alignment with regulatory intent rather than technical satisfiability.
Metadata loss. Attestation artifacts require rich contextual metadata to be interpretable: constraint versions, system identifiers, timestamp references, regulatory source citations, event correlation keys. Metadata loss - whether through storage failures, system migrations, version transitions, or inadequate schema design - degrades evidence artifacts from verifiable records to uncontextualized data. Evidence without adequate metadata cannot support historical compliance reconstruction and may be insufficient for regulatory purposes even if the underlying assertion data is intact. Evidence storage architecture must treat metadata as a first-class retention concern, not as supplementary annotation.
The Role of Attestation in Continuous Compliance
The traditional audit model is periodic. Compliance is assessed at defined intervals, typically driven by regulatory cycles or internal audit schedules. The Attestation Layer's design implies a different model: continuous compliance verification, where compliance state is continuously observable rather than periodically assessed.
Continuous compliance requires the Attestation Layer to maintain current-state evidence at all times. This is architecturally distinct from continuous logging. Logs record events. The Attestation Layer produces structured evidence artifacts from those events - artifacts that are interpretable by external parties without reconstruction. The evidence pipeline must operate continuously, not in batch cycles aligned with audit schedules.
Continuous attestation produces several capabilities that periodic assessment cannot.
Real-time compliance visibility. Internal governance can observe current compliance state without initiating an audit process. Compliance drift - the accumulation of small deviations from constrained behavior - becomes visible as it develops rather than at audit time.
Temporal compliance queries. Stakeholders can inspect compliance state at any point in the evidence history, not only at audit checkpoints. Incident response, regulatory investigations, and internal governance reviews can access point-in-time compliance records without reconstruction.
Enforcement event history. The complete history of enforcement events - every instance where a constraint was evaluated, the result, and the evidence artifact produced - is available for analysis. This history supports constraint tuning, compliance trend analysis, and evidence of sustained compliance over time.
Reduced audit preparation cost. When evidence is continuously organized and maintained in a queryable form, audit response becomes retrieval rather than assembly. The organizational cost of audit preparation decreases as the continuous evidence pipeline takes on the function previously performed by compliance teams assembling evidence at audit time.
The transition to continuous attestation requires investment in evidence pipeline infrastructure that many organizations have not built. The operational model also requires adjustment: compliance functions shift from periodic evidence assembly to continuous pipeline monitoring and evidence quality management. These are genuine transition costs. They do not alter the architectural argument for continuous attestation, but they are part of the honest accounting of what building an Attestation Layer requires.
Liability Boundaries
Infrastructure-generated evidence introduces questions of liability that are not yet fully resolved in most regulatory frameworks. When attestation artifacts produced by automated systems form the evidentiary basis for compliance determinations, and those artifacts prove to be incorrect - due to constraint errors, system failures, or evidence falsification - the question of who bears responsibility requires explicit organizational treatment.
The Attestation Layer does not relocate liability. It changes the evidence basis on which liability is assessed. If an organization presents infrastructure-generated evidence of compliance and that evidence is accurate, the liability position is straightforward. If the evidence is inaccurate, the source of inaccuracy matters.
Constraint errors represent failures in the upstream process that defines what the Control Assertion Engine evaluates. If the constraints are incorrectly specified - if they do not accurately encode the applicable regulatory requirement - the attestation layer will produce accurate evidence of constraint satisfaction while the underlying regulatory obligation remains unmet. Liability for this failure rests with the constraint definition process, not with the evidence system.
System failures represent infrastructure malfunctions that produce incorrect assertion results or corrupted evidence artifacts. Liability for these failures follows standard engineering accountability frameworks.
Evidence falsification represents deliberate manipulation of evidence systems. This is not merely a technical failure. It is potentially a regulatory crime with individual and organizational liability implications that extend well beyond the compliance failure itself.
Organizations deploying Attestation Layer infrastructure must have explicit governance frameworks that address each of these failure modes: who is responsible for constraint accuracy, what engineering accountability applies to evidence system failures, and what controls and monitoring exist to detect and respond to evidence falsification attempts.
Architectural Position in the Compliance Infrastructure Model
The Attestation Layer is the terminal component of the internal compliance evidence pipeline. Its position in the complete architecture is:
Regulatory Requirement ↓ Constraint Lifecycle ↓ Control Assertion Engine ↓ Attestation Layer ↓ External Verification
It receives assertion outputs from the Control Assertion Engine and transforms them into externally verifiable evidence artifacts. It does not generate assertions. It does not evaluate system behavior against constraints. It does not determine compliance outcomes. It performs the evidence structuring, traceability preservation, and integrity protection that make internal assertion outputs useful to external verification processes.
This architectural position defines both the layer's function and its limits. Everything upstream of the Attestation Layer determines what evidence the layer can produce. Constraint quality, assertion engine accuracy, and event logging completeness are all upstream dependencies. The Attestation Layer cannot compensate for deficiencies in these upstream components. It can only structure and protect what it receives.
Downstream of the Attestation Layer are the external verification processes that evaluate evidence and produce compliance determinations. These processes are outside the infrastructure model. They involve human judgment, legal interpretation, and regulatory discretion that infrastructure systems cannot perform or replace.
The Attestation Layer is the evidence interface between a system that produces operational facts and a world that interprets those facts against regulatory and legal standards. That interface must be precise, durable, and honest about its scope. It must produce evidence that is genuinely verifiable, not evidence that is merely persuasive. And it must be explicit about what it does not cover - the oracle boundaries, the constraint assumptions, the legal interpretation gap - so that the external actors who rely on its output can evaluate it accurately.
An Attestation Layer that obscures its limits is not a compliance infrastructure component. It is a liability instrument.